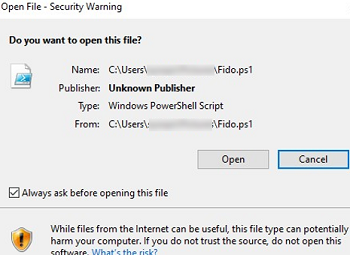
Windows displays a security warning when you try to open or run an executable file/script that you downloaded from the Internet. This article explains how Windows identifies a file downloaded from the Internet and how to unblock it
How Does Windows Know That a File Was Downloaded from the Internet?
All browsers set a special marker in the NTFS metadata (alternate data streams) when downloading a file from the web or from an email. Copying, renaming, or moving files to another NTFS partition does not remove this tag.
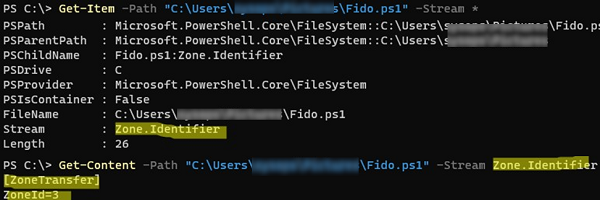
You can use PowerShell to check the alternate streams of a file for the presence of this tag:
Get-Item -Path "C:\downloads\Fido.ps1" -Stream *
In our example, an alternate stream called Zone.Identifier has been assigned to a file downloaded from the Internet. You can get its value:
Get-Content -Path .\Fido.ps1 -Stream Zone.Identifier
[ZoneTransfer] ZoneId=3
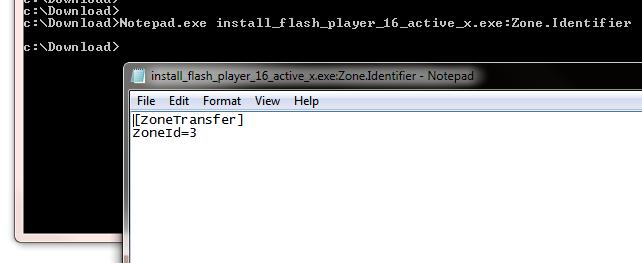
Or like this:
notepad.exe file.exe:Zone.Identifier
The alternate file stream contains the assigned security ZoneId value in the [ZoneTransfer] section. You can find these security zones in the Internet Properties settings in the Control Panel (inetcpl.cpl). Possible zone ID values
- 0 – Local machine
- 1 – Local intranet
- 2 – Trusted sites
- 3 – Internet
- 4 – Restricted sites
In our case, the file in the alternate stream contains the security zoneID=3. This means that the file was downloaded from the Internet. When you open a file, Windows checks the ZoneId attribute. If the file is received from an untrusted source (ZoneId=3 or 4), it will be blocked from being opened (executed).
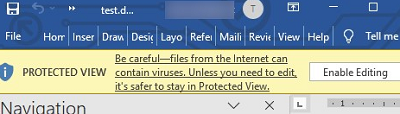
Word also checks for a Zone.Identifier tag on files and opens documents received from the Internet in protected mode.:
Protected view Be careful – files from the Internet can contain viruses. Unless you need to edit, it’s safer to stay in Protected View.
PowerShell: Unblock Files Downloaded from the Internet
You can manually remove this alternate stream marker from the file.
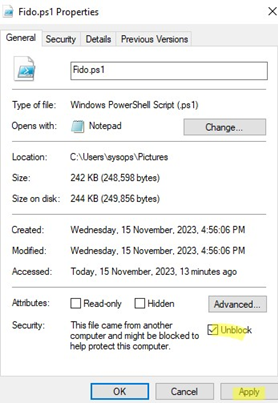
- Open the file properties in File Explorer;
- There should be a note in the Security section:
This file came from another computer and might be blocked to help protect this computer.
- Check the Unblock option and click Apply.
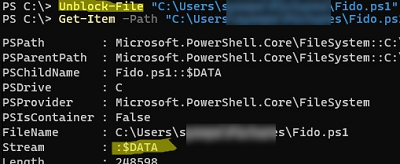
You can also use the PowerShell command to unblock a file that you have downloaded from the Internet:
Unblock-File .\Fido.ps1
Check that the alternate stream has been removed and the file is unblocked:
Get-Item -Path .\Fido.ps1 -Stream *
There should only be one stream left in the file, which is called $Data.
You can manually assign an alternate stream to any file:
Set-Content -Path .\Fido.ps1 -Stream Zone.Identifier -Value '[ZoneTransfer]','ZoneId=3'
You can also remove an alternate data stream from a file like this:
Remove-Item -Path .\Fido.ps1 -Stream Zone.Identifier
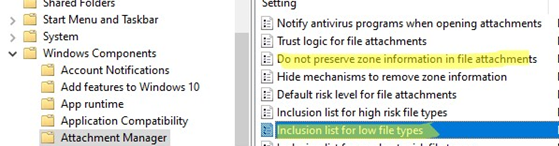
You can enable the option Do not preserve zone information in file attachments in the Local Group Policy Editor to stop blocking files downloaded from the Internet from opening (User Configuration -> Administrative Templates -> Windows Components -> Attachment Manager). However, this is not recommended as it reduces the security of your computer.
It may be even better to make an exception for certain file extensions (with the GPO option Inclusion list for low file types).

2 comments
Very interested and useful, thank you! I was wondering why IE7 blocked images and internal links from my own downloaded html file, and Zone.Identifier was the answer.
“Actually, Windows doesn’t have any tools to deal with the alternative data streams”
Today we have unblock-file cmdlet in Powershell.