Group Policy Object (GPO) is a Windows feature for centrally configuring operating systems, users, and applications. Group Policies allow you to apply the same settings to all users and computers in an Active Directory domain by providing a set of rules and settings for the Windows environment. You can use Group Policy to set Windows configuration, change security settings, configure the user’s environment, install a program or run a script, etc.
Group Policy Architecture and Components
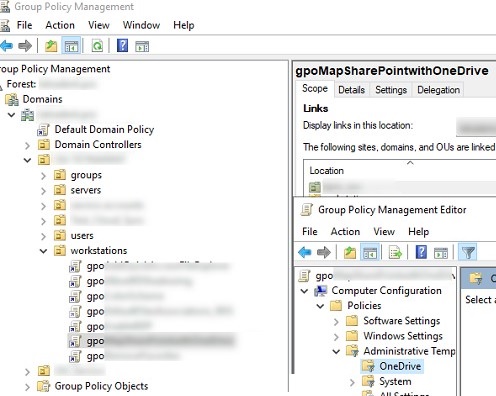
- GPO – a Group Policy Settings object, which contains a set of settings that you want to apply to workstations, servers and/or users. Each GPO in a domain has its own unique GUID. Its files are stored in the SYSVOL directory on Active Directory domain controllers (
\\woshub.com\SYSVOL\woshub.com\Policies\GPO_GUID). All AD domain controllers replicate the GPO folder in Sysvol; - Client computers – Clients retrieve GPO files from domain controllers and apply settings to Windows and users. The process of obtaining and applying a GPO is called a Group Policy Update;
- Group Policy Administrative Templates (ADMX files) are the XML template files for the GPO Editor. ADMX files contain the definitions of the policy settings, which describe what settings can be configured and what their valid values are. Third party developers and administrators can create their own ADMX templates. If you want to support multiple languages in ADMX, you can use ADML files. You can install and update administrative templates for a wide range of applications and services. For example, you can use ADMX templates for Microsoft Office, to configure the settings of the Google Chrome browser, manage LAPS, etc. In a Windows domain, we recommend that you create a central Administrative Template store for ADMX files called PolicyDefinitions.
- Linking GPO – a configured GPO can be assigned to an entire domain, an Active Directory site, or an Organizational Unit in the AD tree structure;
- GPO Security Filtering and WMI Filters allow you to limit the scope of a GPO to specific computers, users, and groups;
- Group Policy Preferences – a built-in set of client extensions that extend the capabilities of GPO (available in Windows Server 2008 and later).
There are two default GPOs created in the domain:
- Default Domain Policy – Assigned to the root of the domain and contains basic settings for all users and computers. It includes domain password policy settings, account lockout, and Kerberos settings.
- Default Domain Controller Policy – contains the basic and auditing settings for the Active Directory domain controller.
Group Policy Management Tools
- Local Group Policy Editor (
gpedit.msc) MMC console –used to configure the GPO settings on the local Windows computer. By default, the gpedit.msc console is only available in Pro/Enterprise editions of Windows, but you can also install it in Home editions. Different local GPO settings can be applied to different groups of users using MLGPO (Multiple Local Group Policy). You can use the LGPO.exe tool to export (backup) the local GPO settings and transfer them to other computers. - Domain Group Policy Management MMC console (
gpmc.msc) used to centrally manage Group Policies at the AD domain level. Allows you to apply GPOs to all computers/users in a domain, to objects in a specific OU, or to specific groups of users or computers. - PowerShell Group Policy module allows you to create, delete, link, unlink, and configure GPO settings from the PowerShell command prompt.
MostUsefulGPOExamplesandBestPractices
- Deploy software (MSI packages) on Windows via Group Policy
- Managing Windows Defender Firewall rules with GPO
- Configure folder redirection using GPO
- How to implement Group Policy to block USB devices
- Disable legacy TLS 1.0 and TLS 1.2 protocols on Windows
- Display system information on the Windows desktop with BgInfo
- Deploying new fonts on Windows via GPO
- How to save BitLocker recovery keys to Active Directory
- Set screen lock for inactivity via Group Policy
- Disable NTLM on Windows
- GPO: run startup or logon PowerShell scripts on Windows
- Enable WinRM and PowerShell Remoting through GPO
- Enable RDP on Windows computers with Group Policy
- Configuring proxy server settings in Windows using Group Policy
- Disable NetBIOS and LLMNT protocols on Windows
- Update trusted root certificates on Windows and add SSL certificate to the trusted ones with GPO
- Configure User Account Control (UAC) settings on Windows with GPO
- GPO: Set WSUS client configuration in Active Directory domain
Examples of using Group Policy Preferences:
- Create a scheduled task on Windows with GPO
- How to add, change, or remove registry keys/parameters using Group Policy
- Mapping network drives with Group Policy
- Copy files or folder to domain computers using GPO
- Create desktop shortcuts using Group Policy
- How to add local administrators via Group Policy
- Connecting shared printers to domain computers and users with GPO