Despite the fact that the Windows XP OS support is over 4 years ago, many customers continue to use this OS, and it seems that nothing will drastically change in the nearest future :(. Recently I found a problem: Windows XP RDP clients cannot connect through the remote desktop to the newly deployed Remote Desktop Services farm on Windows Server 2012 R2. A similar problem occurs when connecting over RDP from Windows XP to Windows 10 1803.
Unable To Connect Remote Desktop from Windows XP to Windows Server 2016/2012R2 and Windows 10
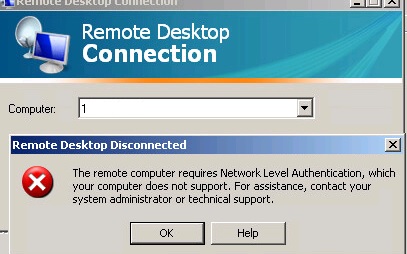
Windows XP users have complained about such RDP client errors as:
To resolve this issue, verify if the latest version of the RDP client is installed on computers running Windows XP. Currently, the maximum version of RDP client that can be installed on Windows XP is RDP 7.0 (KB969084 – https://blogs.msdn.microsoft.com/scstr/2012/03/16/download-remote-desktop-client-rdc-7-0-or-7-1-download-remote-desktop-protocol-rdp-7-0-or-7-1/). You can install this update only on Windows XP SP3. Installing RDP client version 8.0 or later is not supported on Windows XP. The problem was solved after installing this update for a half of the XP clients. The second half of the clients were still facing the issue….
Disabling RDP Network Level Authentication (NLA) on RDS Windows Server 2016/2012 R2
After studying the issues of RDS server based on Windows 2012 R2, we have found that Windows Server 2012 (and higher) requires mandatory support of NLA (Network Level Authentication). If the client doesn’t support NLA, it won’t be able to connect to the RDS server. Similarly, NLA is enabled by default when you turn on the Remote Desktop in Windows 10.
There are two conclusions from the above – to allow the rest WinXP clients to connect to the RDS farm on Windows Server 2016/2012 R2 or Windows 10 via RDP, you have to:
- Disable the NLA check on the servers of the Remote Desktop Services 2012 R2/2016 farm or in Windows 10 workstation;
- Or enable NLA support on the Windows XP clients.
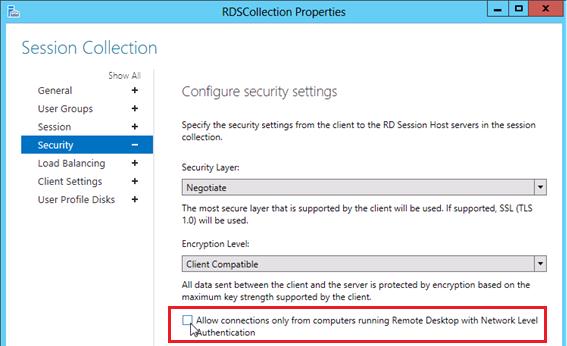
To disable mandatory use of NLA by clients on Windows Server 2012 R2 RDS, open the Server Manager console and go to Remote Desktop Services -> Collections -> QuickSessionCollection, then select Tasks -> Edit Properties, click Security and uncheck Allow connections only from computers running Remote Desktop with Network Level Authentication.
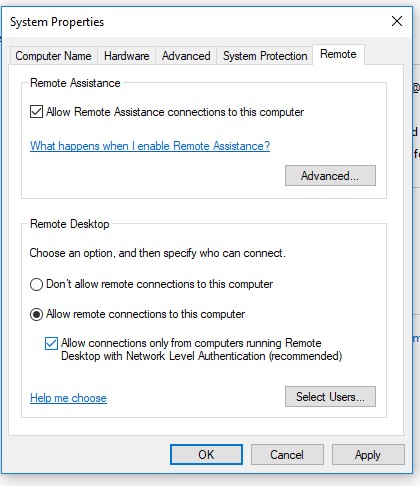
On Windows 10 you can disable Network Level Authentication in the system properties (System -> Remote Settings). Uncheck “Allow connections only from computers running Remote Desktop with Network Level Authentication (recommended)”.
Of course, you need to understand that disabling NLA at the server level reduces the system security and generally is not recommended. It is preferable to use the second method.
Enabling NLA on Windows XP SP3 Clients
You need to install Service Pack 3 on Windows XP to work correctly as an RDP client. If not, you must download and install this update. Service Pack 3 is a mandatory requirement for upgrading the RDP client from version 6.1 to 7.0 and supporting all the necessary components, including the Credential Security Service Provider (CredSS), which is described below.
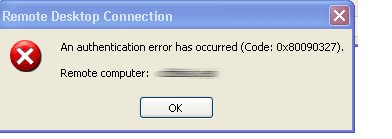
Without CredSSP and NLA support for RDP connection from Windows XP to new versions of Windows, there will be an error:
NLA support appeared in Windows XP starting from SP3, but it is disabled by default. You can enable NLA and CredSSP authentication support only through the registry. To do it:
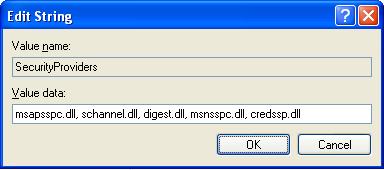
- In the registry key HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders edit the value of SecurityProviders attribute by adding credssp.dll at the end (separated from its current value by comma);
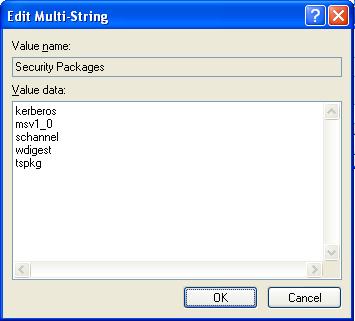
- Then in key HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa add the line tspkg to the value of Security Packages attribute;
- After making these changes, restart your computer.
After these actions are performed, a computer with Windows XP SP3 should easily connect to the terminal farm on Windows Server 2016 / 2012 or to the Windows via the Remote Desktop. However, you can’t save the password for RDP connection on the Windows XP client (you must enter the password every time you connect).
Error: CredSSP Encryption Oracle Remediation
In 2018, a serious vulnerability was found in the CredSSP protocol (CVE-2018-0886 bulletin), which was fixed in Microsoft security updates. In May 2018, Microsoft released an additional update that forbids clients to connect to RDP computers and servers with a vulnerable version of CredSSP (see the article: https://woshub.com/unable-connect-rdp-credssp-encryption-oracle-remediation/). After installing this update when you connect to RDP to remote computers without this update, you receive an error: An authentication error has occurred. The function requested is not supported.
Due to the fact that Microsoft doesn’t release security updates for Windows XP and Windows Server 2003, you won’t be able to connect to supported Windows versions from these outdated operating systems.
To enable RDP connections from Windows XP to the updated Windows 10/8.1/7 and Windows Server 2012/2012 R2/2012/2008 R2, you must enable the Encryption Oracle Remediation policy on the side of the RDP server (Computer Configuration -> Administrative Templates -> System -> Credentials Delegation). Change the policy value to Mitigated, which is not safe as you understand.
6 comments
i didnt find SecurityProviders in the registry directory
Check registry path again or try create it manually
Thanks.
Great! TNX a lot!!!!
Brilliant! Worked for me, so thanks a million !
Thak you so much for sharing – it works !