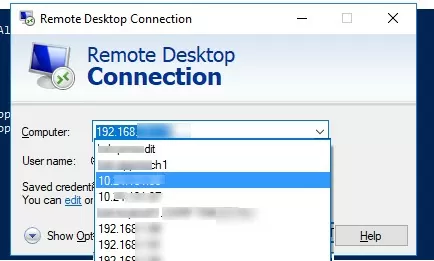
The built-in Windows Remote Desktop Connection client (mstsc.exe) saves the remote computer name (or IP address) and the username that is used to log in after each successful connection to the remote RDP host. The next time the RDP client starts, the user can select one of the saved connections, and the previous username is automatically inserted. If you are using a public computer or a computer you don’t trust, you may want to clear your RDP connection history for security reasons.
This article describes where Windows stores Remote Desktop connection history and credentials, and how to clear RDP history and logs.
Delete the History of Remote Desktop Connections on Windows
Windows stores the history of Remote Desktop client connections in several different places, and to completely clear the RDP history you will need to delete the data from all of these places.
How to Delete RDP Connection History from Registry
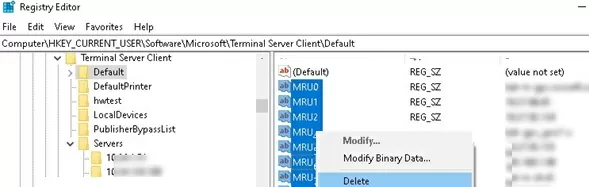
- Open the Registry Editor (
regedit.exe) and go to the reg key HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client; - The Default subkey contains history entries for the last 10 RDP connections. The names of the parameters are MRU0-MRU9 (MRU – Most Recently Used). Their values contain IP addresses/RDP host names. Select all the registry parameters in the key and delete them;
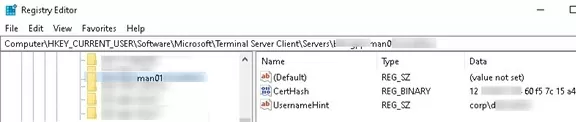
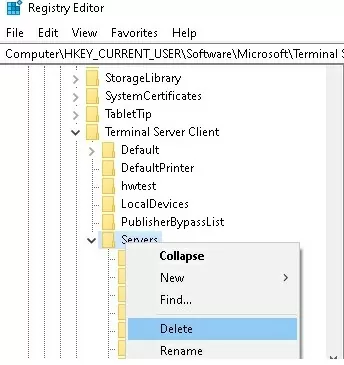
- Then expand the Servers subkey. A list of all previously used RDP hosts and user accounts is stored here. The username is contained in the UsernameHint parameter. This username is automatically inserted into the mstsc.exe client window when you connect to this RDP host. The CertHash parameter contains the thumbprint of the server’s RDP certificate (see: “Configuring trusted TLS/SSL certificates for RDP“);
- Clear all entries in the Servers registry key. The easiest way to do this is to simply delete the entire Servers reg key, and then re-create it manually.
Delete the Default.RDP File
Then delete the hidden Default.rdp file from the %userprofile%\Documents folder in the user profile. This file stores information about the last RDP connection.
How to View and Clear RDP Event Viewer Logs in Windows
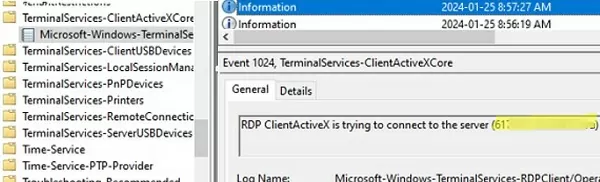
The RDP client also logs each outbound connection to the Event Viewer log (Applications and Services Logs -> Microsoft -> Windows -> TerminalServices-ClientActiveXCore -> Microsoft-Windows-TerminalServices-RDPClient/Operational).
To list the log for outbound RDP client connections, use the Get-WinEvent cmdlet to select and filter the events in the Event Viewer:
$properties = @(
@{n='TimeStamp';e={$_.TimeCreated}}
@{n='LocalUser';e={$_.UserID}}
@{n='Target RDP host';e={$_.Properties[1].Value}}
)
Get-WinEvent -FilterHashTable @{LogName='Microsoft-Windows-TerminalServices-RDPClient/Operational';ID='1102'} | Select-Object $properties
You can clear this event log from the Event Viewer console or by using the command:
WevtUtil cl Microsoft-Windows-TerminalServices-RDPClient/Operational
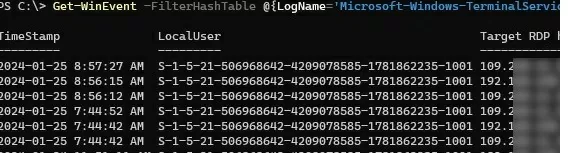
Delete Recent RDP History Entries from the Start Menu and Taskbar
Windows also stores recent remote desktop connections in Jump Lists. If you type mstsc in the Windows search box or right-click on the client in the taskbar, you will see the history of previous RDP connections in the Recent list.
To clear the RDP history in the Start Menu and Jump Lists, clear the Recent Items list by deleting the files in the %AppData%\Microsoft\Windows\Recent\AutomaticDestinationsdirectory.
Script to Clear RDP Connection History
To quickly clear the history of RDP connections in Windows, you can use a batch script. This script will automatically perform the manual actions described above to clear the connection history and the RDP logs.
@echo off
reg delete "HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\Default" /va /f
reg delete "HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\Servers" /f
reg add "HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\Servers"
attrib -s -h %userprofile%\documents\Default.rdp
del %userprofile%\documents\Default.rdp
del /f /s /q /a %AppData%\Microsoft\Windows\Recent\AutomaticDestinations
A similar PowerShell script to clear all entries in the RDP connection history:
Get-ChildItem "HKCU:\Software\Microsoft\Terminal Server Client" -Recurse | Remove-ItemProperty -Name UsernameHint -Ea 0
Remove-Item -Path 'HKCU:\Software\Microsoft\Terminal Server Client\servers' -Recurse 2>&1 | Out-Null
Remove-ItemProperty -Path 'HKCU:\Software\Microsoft\Terminal Server Client\Default' 'MR*' 2>&1 | Out-Null
$docs = [environment]::getfolderpath("mydocuments") + '\Default.rdp'
remove-item $docs -Force 2>&1 | Out-Null
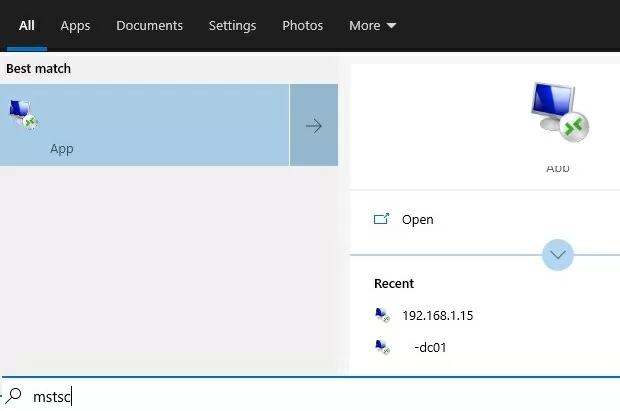
How to Clear Remote Desktop Bitmap Cache?
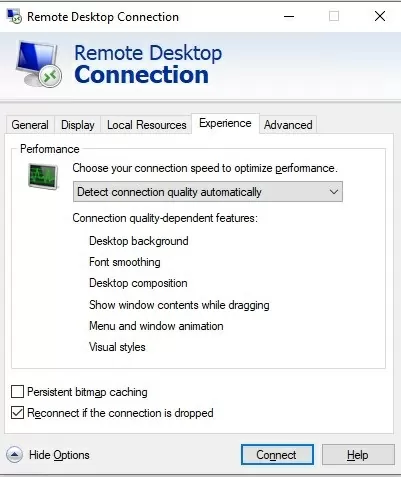
By default, the mstsc.exe client caches rarely modified areas of the remote desktop as bitmaps (persistent bitmap caching). The RDP client cache can significantly reduce network traffic.
The RDP client cache is stored in *.bmc and *.bin files in the %LOCALAPPDATA%\Microsoft\Terminal Server Client\Cachefolder.
The RDP cache contains raw bitmaps of the RDP screen in the form of 64×64 pixel tiles. Attackers can use simple PowerShell or Python scripts (easily searched using the RDP Cached Bitmap Extractor query) to capture large areas of the remote desktop from cached PNGs.
For security reasons, it is recommended that you clear the RDP cache folder and prevent the RDP client from saving the screen image to the cache. Disable the Persistent bitmap caching option on the Advanced tab of the Remote Desktop Connection client.
How to Prevent Windows from Saving RDP Connection History
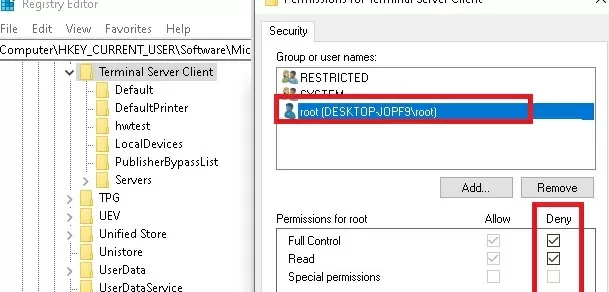
If you do not want Windows to store the history of RDP connections, you must deny writing to the HKCU\Software\Microsoft\Terminal Server Client registry key. The first step is to disable the inheritance of permissions on the specified reg key (Permissions -> Advanced -> Disable inheritance). Then change the ACL of the registry key by selecting the Deny for users (but you should be aware that this is an unsupported configuration).
As a result, mstsc.exe is simply not able to write any RDP connection information to the registry.
Remove Saved RDP Credentials on Windows
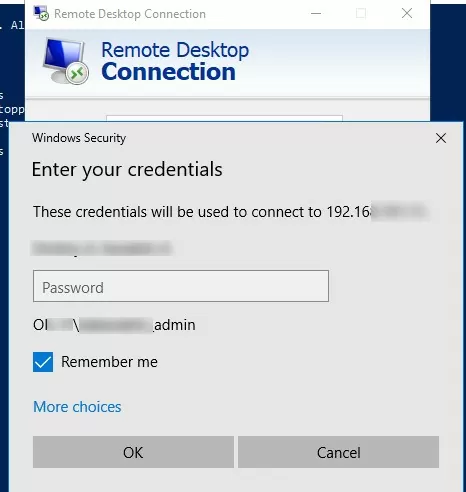
The RDP client allows you to store the user’s password in the built-in Windows Credential Manager and automatically connect to a remote host without entering a password.
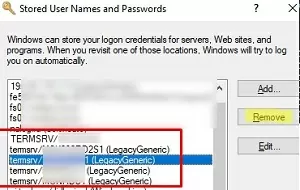
You can delete saved RDP passwords from the Credential Manager window (run the command rundll32.exe keymgr.dll,KRShowKeyMgr ). Remove all entries prefixed TERMSRV\.
Or you can clear the stored credentials for RDP with the command:
For /F "tokens=1,2 delims= " %G in ('cmdkey /list ^| findstr "target=TERMSRV"') do cmdkey /delete %H
10 comments
Thanks for your post. I was looking to clear the last connection, and deleting the default.rdp file helped in that regard. Thanks again!
I am still getting the username once I login to the RDP
go to “Documents” folder and delete “Default.rdp”
In windows 10 there is still a recent connection list when you search RDP in bottom search bar and it brings the RDP client app in the result. How to clear that too?
Thanks, it worked.
still leaves sum info on the resents on windows 10
Is there a way to prevent RDP from caching remote computer name
I do not want RDP to cache remote computer name at all
Thanks for publishing this forum. It was very helpful to me.
Thanks, the script worked and saved a lot of time
Hello,
This batch file does not work on Windows 11. Is there a way to make it work on Windows 11? Please help me out. Please