When started, some programs require permission elevation (the shield next to the app icon), but actually, they don’t need administrator privileges for their normal operation. For example, you can manually grant permissions for your users on the app folder in the ProgramFiles and/or registry keys used by the program. If the User Account Control is enabled on the computer, a UAC prompt will appear and Windows will ask the user to enter the administrator password if you try to run such a program as a standard user.
To bypass this mechanism, many admins simply disable UAC or grant admin rights by adding a user account to the local group “Administrators”. Of course, both methods are not safe. Neither of these methods is recommended for widespread use because they reduce Windows security. In this article, we will look at how to run a program that requires administrator permissions as a standard user and suppress the UAC elevation prompt.
- Configure Permissions for Non-Admin Users to Run a Program
- Allow Standard Users to Run a Program That Requires Admin Privileges
- How to Bypass UAC with the RunAsInvoker Option in CMD?
- Enable the RunAsInvoker Mode in the EXE File Manifest
- Create a Shortcut to Run the Program with a Saved Administrator Password
Configure Permissions for Non-Admin Users to Run a Program
A Windows program may ask you for administrator permissions when it starts if:
- The program needs to access a system directory or a file for which the NTFS permissions have not been granted to non-privileged users;
- If the program was compiled with a special flag that requires elevation at startup (
requireAdministrator).
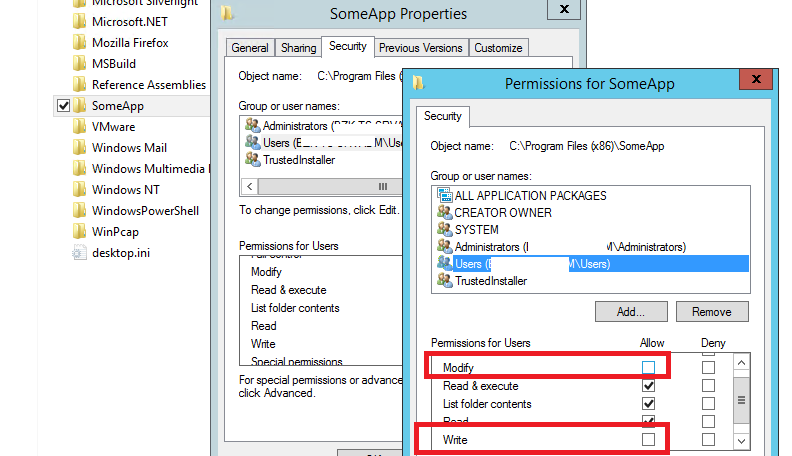
In the first case, all that is required to solve the problem is to grant the RW or Full Control user permissions to the program directory or the required system directory/file. For example, a program stores its files (logs, configuration files, etc.) in its own folder in C:\Program Files (x86)\SomeApp or some system directory. The user must have permission to write to these files for the program to work correctly. In order for this program to work normally, administrator permissions are required.
To allow the program to run as a non-admin user, it is sufficient to manually grant the user (or the built-in Users group) the permission to modify/write a file/directory at the NTFS file system level
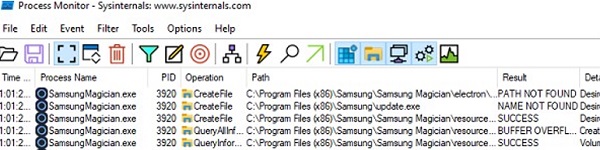
To find a list of files, folders, and registry keys that the program is accessing, use the Process Monitor (https://learn.microsoft.com/en-us/sysinternals/downloads/procmon). Enable the filter by the name of the program process and find all the resources, if you try to access them, Access Denied is displayed. Grant the necessary permissions to folders/files/registry keys.
Allow Standard Users to Run a Program That Requires Admin Privileges
Earlier we described how to disable a UAC prompt for a specific program using the RunAsInvoker parameter. However, this method is not flexible enough.
Let’s look at a simpler way to force any program to run without administrator privileges (without entering the admin password) and with UAC enabled (Level 4, 3, or 2 of the UAC slider).
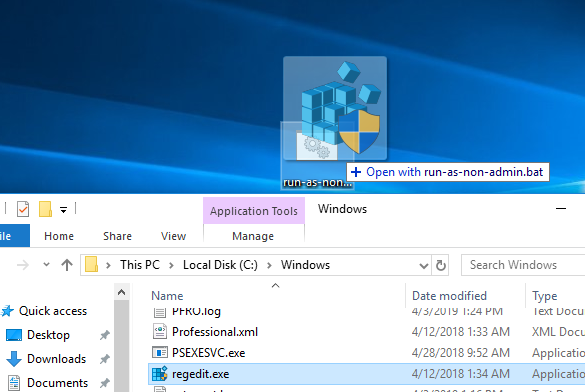
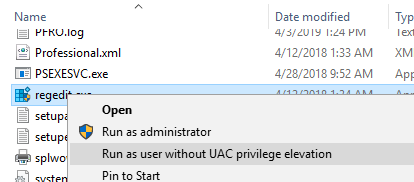
Let’s take the Registry Editor as an example — regedit.exe (it is located in the C:\Windows\ folder). Notice the UAC shield next to the app icon. This icon means that UAC elevation is required to run this application.
When you run regedit.exe, you will see a User Account Control prompt asking for the administrator credentials (Do you want to allow this app to make changes to your device?). If you do not provide a password and do not confirm elevation, the app won’t start.
Let’s try to bypass the UAC request for this program. Create the text file run-as-non-admin.bat containing the following code on your Desktop:
cmd /min /C "set __COMPAT_LAYER=RUNASINVOKER && start "" %1"
To force the regedit.exe to run without administrator privileges and to suppress the UAC prompt, simply drag the EXE file you want to run to this BAT file on the desktop.
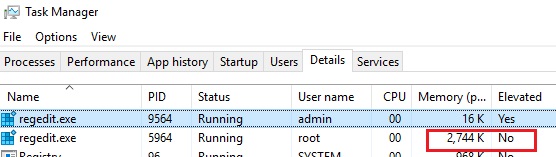
The Registry Editor should start without a UAC prompt and without entering an administrator password. If you open the Task Manager and add the Elevated column, you will see that there is the regedit.exe process without the elevated status (run with non-admin user permissions).
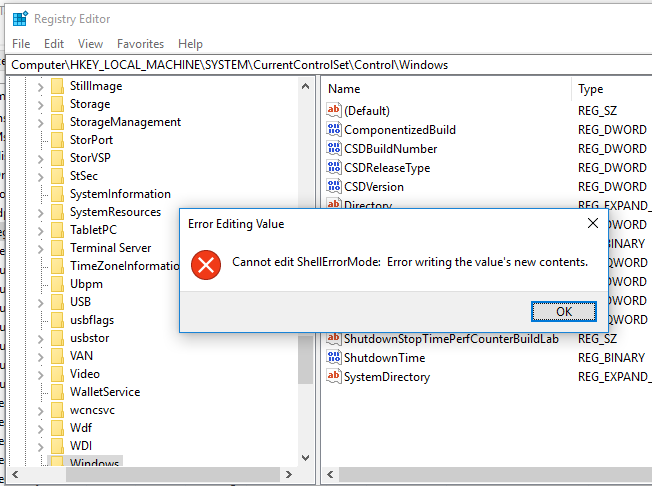
Try to edit any item under the HKEY_LOCAL_MACHINE registry hive. As you can see, a user cannot edit the item in this registry key (the user doesn’t have write permissions for the system registry keys). However, you can add or edit registry keys and parameters in your user hive (HKEY_CURRENT_USER).
In the same way, you can run any app using the BAT file. Just specify the path to the executable.
run-app-as-non-admin.bat
Set ApplicationPath="C:\Program Files\SomeApp\testapp.exe"
cmd /min /C "set __COMPAT_LAYER=RUNASINVOKER && start "" %ApplicationPath%"
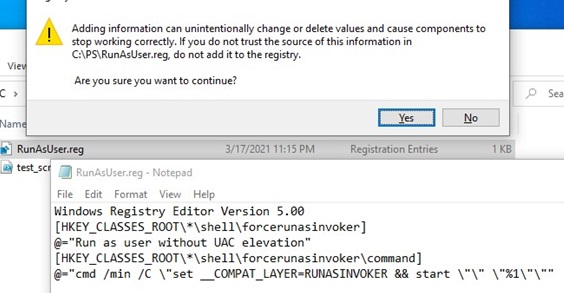
You can also add a context menu that allows running all apps without elevation. To do it, create the RunAsUser.REG file, copy the following code into it, save, and import it into the Windows registry by double-clicking on the reg file (you will need administrator permissions to apply this change).
Windows Registry Editor Version 5.00 [HKEY_CLASSES_ROOT\*\shell\forcerunasinvoker] @="Run as user without UAC privilege elevation" [HKEY_CLASSES_ROOT\*\shell\forcerunasinvoker\command] @="cmd /min /C \"set __COMPAT_LAYER=RUNASINVOKER && start \"\" \"%1\"\""
After that, to run any application without administrator privileges, just select “Run as user without UAC privilege elevation” from the Windows File Explorer context menu.
RUNASINVOKER mode for the program won’t allow you to elevate the permissions. The RunAsInvoker suppresses the UAC prompt and tells the program that it should run with the current user’s privileges, and not ask for the elevation of privileges. If a program really needs elevated privileges to edit system settings or files, it won’t work or will ask for admin permissions again.How to Bypass UAC with the RunAsInvoker Option in CMD?
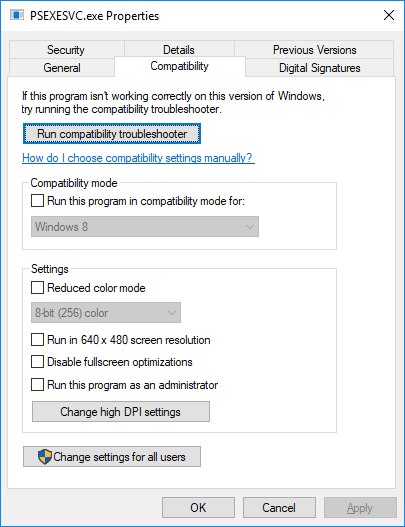
The __COMPAT_LAYER environment variable allows you to set different compatibility levels for the applications (the Compatibility tab in the properties of an EXE file). This variable allows you to specify the compatibility settings with which you want to run the program. For example, to start an app in Windows 8 compatibility mode with a 640×480 resolution, set the following:
set __COMPAT_LAYER=Win8RTM 640x480
The __COMPAT_LAYER variable has some options that we are interested in. There are the following parameters:
- RunAsInvoker – run an app with the privileges of a parent process without a UAC prompt;
- RunAsHighest – run a program with the highest-level permission available to the user (the UAC prompt will appear if a user has administrator privileges);
- RunAsAdmin – run an app as administrator (the UAC prompt will always appear).
The following commands enable the RunAsInvoker mode for the current process and run the specified program without elevation:
set __COMPAT_LAYER=RUNASINVOKER
start "" "C:\Program Files\MyApp\testapp.exe"
Enable the RunAsInvoker Mode in the EXE File Manifest
As mentioned above, Windows displays the UAC shield icon for programs that require elevated privileges to run. Developers set this requirement when compiling the application in the program manifest
You can edit the manifest of any EXE file and disable the requirement to run the program in elevated mode.
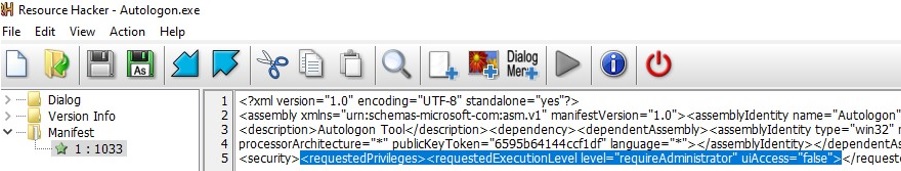
Use the free Resource Hacker tool to edit the program manifest. Open the program executable in Resource Hacker.
Autologon.exe tool by Sysinternals, which can be used to automatically log into Windows without a password. In the tree on the left, go to the Manifest section and open the program manifest. Pay attention to the following XML section:
<requestedPrivileges> <requestedExecutionLevel level="requireAdministrator" uiAccess="false"/> </requestedPrivileges>
With the requireAdministrator option enabled, Windows always runs this program with administrator rights.
Change requireAdministrator to asInvoker and save changes to the .exe file.
Note that now the UAC shield has disappeared from the program icon, and you can run it as the current user without asking for the administrator password.
In this case, you can force the program to use an external manifest file. Create a plain text file appname.exe.manifest (for example, Autologon.exe.manifest) in the directory with the exe file and copy the manifest code from Resource Hacker into it. Replace requireAdministrator with asInvoker. Save the manifest file.
To make Windows always try to use an external manifest file when starting EXE files, enable a special registry parameter:
REG ADD "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\SideBySide" /v PreferExternalManifest /t REG_DWORD /d 1 /f
Restart Windows and make sure that the program is using an external manifest file and is running without administrator privileges.
Create a Shortcut to Run the Program with a Saved Administrator Password
If the methods of running a program with the RunAsInvoker flag do not work for your legacy application, you can try to run such an app in a user session using saved administrator credentials. This is the least secure way to run programs without granting the user local administrator privileges, so we have deliberately left it last.
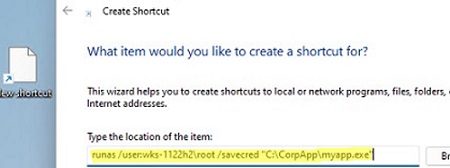
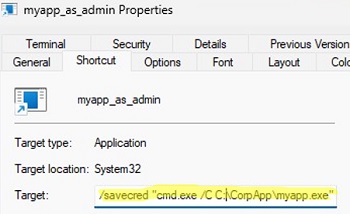
To open the program, create a new shortcut on your desktop. Specify the computer name, the local administrator name, and the full path to the target app executable.
For instance:
runas /user:wks-123\root /savecred "C:\CorpApp\myapp.exe"
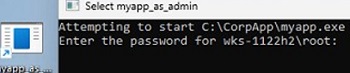
When you run the program for the first time, it will open a command prompt in which you will be asked to enter the administrator password.
The RunAs command, when run with the /SAVECRED option, saves the username and password to the Windows Credentials Manager.
The next time the shortcut is run, the runas tool will automatically get the saved password from Credentials Manager and use it to run the app under the specified local administrator account (you won’t be prompted for the password each time you open the shortcut).
The following command lists saved passwords in Credential Manager:
RunDll32.exe keymgr.dll,KRShowKeyMgr
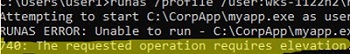
An error occurs when launching such a shortcut on Windows 11:
RUNAS ERROR: Unable to run - C:\CorpApp\myapp.exe 740: The requested operation requires elevation.
To fix this, change the command in the shortcut properties. Replace it with:
C:\Windows\System32\runas /profile /user:WKS-123\root /savecred "cmd.exe /C C:\CorpApp\myapp.exe"
Using the /savecred option is not secure, as we mentioned above. This is because a user who has the administrator password saved in their profile can use it to run any program or command with elevated permissions, or even to reset the administrator account password. Passwords stored in the Credential Manager can also be dumped in plain text by tools such as Mimikatz, so it is better to disable the use of saved passwords.
There are several third-party tools that allow you to work around the drawback of using a stored admin password in runas. For example, AdmiLink, RunAsRob, RunAsSpc. These apps allow you to store the encrypted administrator password and safely run the program with administrator privileges. These tools will not allow the user to run any application or command with saved credentials because they check the path and checksum of the executable file when it starts.


76 comments
Are you able to help me?
I cannot import the .REG file without having to use an admin Registry Editor, it gives me an error otherwise.
Thanks
Use the bat file to run your application (instead of the reg file that should be imported into the registry).
So you have to drag and drop your application everytime to launch it?
The whole point is to remove the extra step of clicking yes on the UAC prompt, not replace that with a different step of dragging and dropping.
It is still not working
omg this was way more simple than i thought it would be. used it to run a screen recorder! thanks 😀
What if The software you Installed is Requesting to Run as a Administrator What am I supposed to do now?
hey can u tell me on how to download davinci resolve 16/17 with these methods pls
Can you also install an exe with this method and then freely use it without dragging and dropping?
Peter, did you ever figure out how to get this working?
they never respond lmfao and i wont too
Thanks! This article helped me in more ways than you can imagine!
Doesn’t work, it still prompts for admin credentials
It doesn’t work for all .exe or all setup.exe files.
.bat files say this app can’t run on your pc for me
Different problem, maybe a 32bits program running on 64bits computer or reverse, or maybe you need the compatibility mode (try the troubleshooter)
Doesn’t work. Still requires root password for a given .EXE
Idiot, it doesn’t work for all .exe or all setup.exe files.
No need for insults ya smelly fish man. Perhaps you could elaborate as to why it doesn’t work for some while it works for others? Or maybe just don’t comment at all.
It’s great to get rid of the UAC prompt for specific programs but I still need a way to allow Windows 10 users who only have standard rights to run some legacy applications that require administrative rights to use the program.
You may be able to do what you need using the Task Scheduler method. Look it up, as it will allow you to run a program with elevated privileges.
Same as me. Scheduler doesn’t work anymore. Now I use the tool Runasrob to run an application as administrator with standard user rights.
Where in the registry do you import the REG file? Help pls
HKEY_CURRENT_USER
Ok, so in “HKEY_CURRENT_USER”: in which specific folder do we need to import the REG file?
In any case, the system blocks the operation by sending me “Imbossible to import… Error during the access to system registry”. So what can I do?
I have the same problem
Hello, Thanks a lot, this is really helpful and amazing for me.
Also, I would like to know after I installed the program but I can’t uninstall or delete some programs that have require permission (shield on the app icon).
Could you please share the method to uninstall without Admin Privileges and to Bypass UAC Prompt, please?
Thanks again.
I think it is impossible. You cannot uninstall a correctly registered program without admin permissions.
But you can try the following:
1) Find the name of toyr app name in the reg key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall (just browse through each sub key)
2) Locate the GUID of your application: for example {0000000-1111-2222-3333-4444444444444}
3) Create a bat file uninstallapp.bat with the code: msiexec.exe /x {0000000-1111-2222-3333-4444444444444}
4) Run the uninstallapp.bat file with bypass UAC according with this article
works very well, thanks ….. apart from a dll error that I am getting during the installation process
it says error: access to path denied C:\\WINDOWS\METASETUP.dll is denied
any suggestions please ?
The installer really needs elevated permissions to access this file. You can change the NTFS permissions for the file under admin account using the ICACLS tool or via File Explorer. Grant Read/Write permissions for your non-admin user.
not working still askin for yes no prompt for uac
Im Not Sharing My Real Name but i will say its good
Are you Geronimo ?
nope he is g4y
Big brain man here.
Where in the registry do you import the REG file? Help pls
HKEY_CURRENT_USER
right click the reg file, run as admin
If you or any of the others are talking about RunAsUser.REG, you need to be an administrator *first*. Then “run as admin” will work to import the reg file. The appropriate registry paths are specified inside the reg file.
This goes for anyone complaining these methods “don’t work” – they’re for an ADMINISTRATOR to allow “normal” users to do various tasks (where the user already has the appropriate permissions).
To run a program actually as an administrator (such as any setup.exe/installer program that modifies the operating system as a whole), you need to use the very last method or the other tools mentioned at the end to run the task with an actual administrator account (using admin credentials that have been stored in some manner not accessible to the user).
worked perfect thanks a lot
Hello.
I want to activate “Direct Play”.
I manage to access “OptionalFeatures.exe” with the first and 2nd method, but a message is displayed: “an error has occurred. Some functionality has not been modified correctly”.
And with the 3rd method, a message appears: “Unable to import … registry access error”.
Can you help me please?
This program does not have a program associated with it for performing this actions, i cannot run without admin rights nor use recovery media and installation disk. WELP!
…and when going to user accounts said im an admin, confused and dead someone got any solutions!
Not the good type of admin maybe… This happened to me once, I activated default admin account (google it pls I can’t now)
I need some help with this.
I need to run this app as an administrator.
Any way to fix it?
How to make admin regedit shortcut win 10?
Hello, got the Run as admin.bat file and I copied the code, but when I drag it on top of the System Config App, it still asks for the admin password. I think it might be because the .bat file is actually a text document. Could someone please help me with this? I am trying to get into the System Config so I can disable my Microsoft Family restrictions.
go to the files app and at the top select view and then in the top right will be 3 check boxes, u want to click “File Name Extensions” , now rename it to a .bat and it will change
Bruh the bat file isnt even working it doesnt show gear as it icon its still showing a text icon what to do please help im so close ;(
Okay fixed it but here my new question now what do we save the bat file as and how do we use it to open the uac application, do we have to find the applications exe and use the bat file on the exe to open it?
Should we save as a txt or to all files?
Save it to all files and in the name you have to put .bat
Helpful? If not let me know
I cant find registry editor’s exe, sorry for so many comments im not much of a computer expert :/
Ok most of my probelms have been sovled now my last question is: after putting in the code in the text document do we have to save it as run as non admin,bat afterwards then do we save it to all files instead of txt? bc its still not working idk why rlly
I did all of the steps but its still not working what do you guys think the problem is
so it still making me enter in admin information. is there something that i may have done wrong or a way around this
I have a custom uninstaller that is registered in current user Uninstall. From what I observed so far, uninstallers registered like this are always launched as admin.
I want my uninstaller to be launched as the current user because it needs to remove some current user registry keys. And if the uninstaller is run as another user (who is admin), then it will try to delete from the wrong current user keys.
I noticed that in the Uninstall key I can specify as a value the uninstall string which currently is simply the path to my custom uninstaller.
Work fine for me, not for all but its work for some
Please Give Me Video I Can Follow By That.
None of these Methods Work for CurseForge 🙁
hey im trying to install bittorrent without admin password but as soon as i run it with the batch file it just shows the place where im supposed to put the admin password, what should i do??
I’m trynna get blender on my school computer but everything I try doesn’t work. It keeps saying this app has been blocked by the admin. I’m going to keep trying but pls, can anybody help? If so I would appreciate it so much.
School administrators often (and should) have policies that stop random users from installing unapproved/unlicensed software on school computers. This is for a few reasons:
* If the program or computer has problems, the first port of call is often the school IT admins, who have enough problems trying to fix the software that they are actually responsible for. Not random apps someone downloaded from some dodgy source. The school machines have been designed to run with the software provided on them – the hardware itself has been purchased with “typical use” in mind, for as cheaply as possible while still being decent to use.
* Even if you’re installing legit software from a legit vendor, you probably have not paid a license fee for it. Or, if you have, you haven’t paid the right kind of license fee for it to be installed on a computer that belongs to an organisation (not an individual). Organisations can and have been sued for software installed on their machines that they have not paid for. Even if the user has a legit license, if that machine doesn’t *belong* to them, they can’t just transfer the license to a third party. Being sued is EXPENSIVE.
* Most importantly, the way Windows is designed, if you can install any application, you can also download/install malware. Or software with malware embedded in it. it’s absolutely not worth the risk, especially if the machine connects to the school network (which they nearly always do).
For Blender specifically, it is free and open source, great. It also consumes a huge amount of resources, and it may not run properly on a school machine. Or, if it does, it’ll slow everything else down. If you’re submitting an assignment while Blender is rendering and there are timeouts and the assignment is not submitted on the deadline or at all, would you be happy that Blender ate your homework and accept the fail?
If the school equipment/network has an actual fault, the school will get the thing fixed or maybe there will be a later deadline. Telling someone that their unapproved software has caused the issue and it’s too bad for their assignment does not make anyone happy. Thus it’s best to try and avoid any such problems by not allowing random software. (I have worked in places where Blender was actually supplied on certain machines – and those machines were very grunty and in a lab specifically for design students. These days, it might be delivered on a virtual lab machine accessible over the internet, but again it would have a higher spec to run the software.)
Sorry for the long explanation, but it might be helpful to know that those restrictions are not there because any IT administrator wants to be mean (well, some do), but because it honestly requires a lot of time and expense to manage things so that they are as reliable and secure as possible for everyone using the software/equipment for the intended purposes. When we have thousands of machines to look after, we can’t allow unknown stuff to be installed, and especially not allow *anyone* the right to install stuff on the machines – because you can break things more fundamentally than just one piece of software. In some instances, machines might be provided that allow random stuff to be installed, but there it’s “you break, you fix” or the entire machine gets reimaged and your data deleted if something goes wrong.
Hi, thank you for the instructions! I’m just curious — after dragging the .exe to the .bat file (which worked great!), where is the command saved in the .exe file? I don’t see it in the .exe properties like I expected, in the “target” command. Is it inserting the elevated permission in the registry key for the .exe app? Also, can I then delete the .bat file from the desktop and the .exe will continue to run with elevated permissions?
The command isn’t saved at all. What the BAT is doing is simply running “cmd /min /C “set __COMPAT_LAYER=RUNASINVOKER && start “” C:\Path\To\My\ExeFile.exe”. By dragging and dropping the file, all you’re doing is providing the EXE file’s location (e.g. C:\Path\To\My\ExeFile.exe) to that set of commands, which add up to launching the EXE with “RUNASINVOKER” compatibility settings. “%1” at the end of the original command is a placeholder for the EXE path. And it can be used over and over again with any EXE.
If you wanted to skip the drag and drop, you could edit the BAT to provide the EXE path (as in my first example), but you’d need a different BAT file for each EXE you want to run that way. And if you move the EXE, you’d need to update the BAT with the new path for it to continue working.
Thank you so much for this!!!!!!!!!!!!!!!
it works 100% even on domain controlled workstation.
I’ve been googling this for years.
This webpage is really interesting: NONE of the suggestions ever works! It’s pathetic!
it doesnt work, blocked by admin lol.
hi can you help me pls , i have a pc and i am not admin ,the pc belongs to me , i found it and buy it on ebay …The problem is that when i want to do anything like opening cmd as admin it asks me a fingerprint but i hav no fingerprint associated, i also have no yes button but just a no button.
Hi, how to force a process to open with UAC virtualization enabled?
Virtualization supports only 32-bit applications.
Then add the registry entries:
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers]
“C:\\Program Files (x86)\\APP1\\program.exe”=”RUNASINVOKER”
and
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers]
“C:\\Program Files (x86)\\APP1\\program.exe”=”RUNASINVOKER”
hello, dunno if this is still active but i am kinda confused. i am trying to play a game that needs admin privileges to start up and i dont know what to do in that kind of scenario, i am probably just looking over something though.
hi, is it possible to install an application without the administrator detecting it?
Does not work for dism.exe on windows server 2019.
Disabling the “run as different user” in the context menus prevents this bypass from working.
Unless you run the .bat file as an administrator and enter creds, no dice.
From the DOD (Department of Defense) U_MS_Windows_11_V1R5_STIG checklist for hardening Windows 11.
Registry Paths:
\SOFTWARE\Classes\batfile\shell\runasuser\
\SOFTWARE\Classes\cmdfile\shell\runasuser\
\SOFTWARE\Classes\exefile\shell\runasuser\
\SOFTWARE\Classes\mscfile\shell\runasuser\
Type: REG_DWORD SuppressionPolicy
Value: 0x00001000 (4096)
all it works is take out the admin password and the program runs. in my case taskmgr.exe. but when i try to stop a process, it still says i have no admin rights. i want to run task manager as admin so i can stop a process but i don’t have admin password. so annoying.
The method described in this post doesn’t give you local administrator permissions. It simply describes how to remove the UAC elevation prompt for a program that does not actually need administrator rights to run.