When trying to run an EXE, MSI, BAT, CMD, or other executable file type from a local drive or shared network folder in Windows, you may see the Open file – Security Warning. To run the program, the user must manually confirm the launch of the file by clicking the ‘Run‘ button. This Windows security warning usually appears when you open a file downloaded from the Internet, run an executable file from a shared folder or mapped network drive, or run a file with an invalid digital signature.
Windows Security Warning When Launching Executable Files
The security warnings are designed to protect your computer from running potentially dangerous executable files downloaded from the Internet or received from untrusted sources.
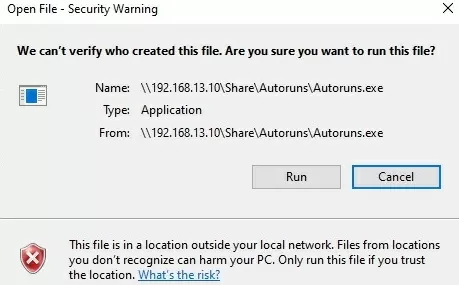
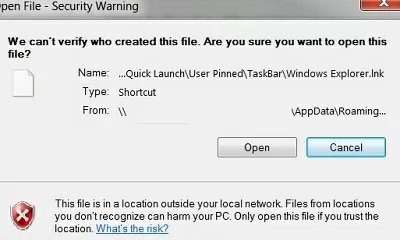
For example, when opening a file from a shared folder, the Windows security alert might look like this:
Open File — Security Warning The Publisher could not be verified. Are you sure you want to run this software? We can’t verify who created this file. Are you sure you want to run this file? This file is in location outside your local network. Files from locations you don’t recognize can harm your PC. Only run this file if you trust the location.
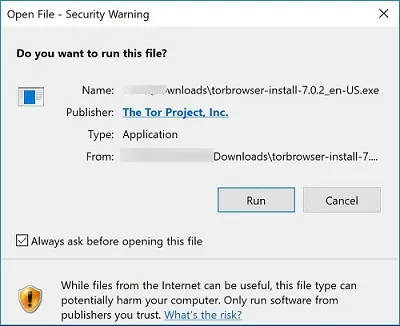
When running a file downloaded from the Internet from a local drive or a network share mounted via net use, the warning message text is slightly different:
Open File — Security Warning Do you want to run this file? While files from the Internet can be useful, this file type can potentially harm your computer. Only run software from publishers you trust.
If you uncheck the Always ask when opening this file option, the security window will not appear the next time you run this file. But in this way, you will have to add programs to the exception list manually.
Let’s try to find out how to disable the security warnings when running executable or installation files on Windows.
If you install or run programs on a user’s computers in the background (through scheduler tasks, Group Policy logon, or SCCM scripts, etc.), this can cause problems. This is because the security warning prompt doesn’t appear in the user’s session in such cases. This makes it impossible to install or run such apps in batch (background) mode.
How to Disable Open File Security Warning for Downloaded Files
The executable files downloaded from the Internet are automatically marked by the browsers as potentially dangerous (downloaded from an unsafe source). This feature is implemented using the alternative NTFS file streams (Alternate Data Streams, ADS). Simply put, it’s a special file mark that is automatically assigned to downloaded files (see the article How does Windows know if a file was downloaded from the Internet). To remove this mark, you need to unblock this file.
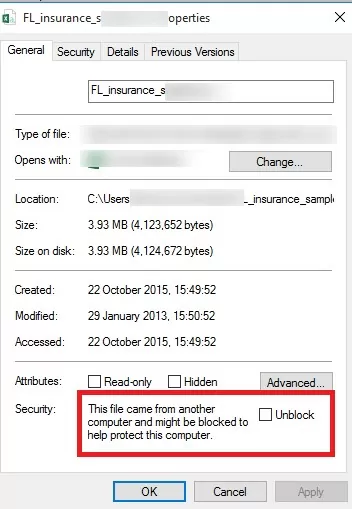
- Open the executable properties
- On the General tab, click the button or tick the Unblock checkbox. The following warning appears next to the button of the file received from the Internet:
This file came from another computer and might be blocked to help protect this computer. - Click OK to save the changes. The file is now unlocked and will open without warning (NTFS alternate data streams removed).
To unblock a file by resetting the alternate NTFS stream Zone.Identifier label the PowerShell command can be used:
Unblock-File C:\Downloads\somefile.exe
In Windows, a special GPO setting can be used to prevent the zone information label from being applied to files downloaded from the Internet: Do not preserve zone information in file attachment (User Configuration -> Administrative Templates -> Windows Components -> Attachment Manager) or create the registry parameter:
reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\Attachments" /v "SaveZoneInformation" /t REG_DWORD /d "1" /f
As a result, files downloaded by browsers (including Edge, Chrome, Firefox, etc.) will not contain the Zone. Identifier stream label.
Security Warning When Opening Files from a Network Share
A security warning prompt also appears when opening executable files from a shared folder accessed via a UNC path that includes an IP address or FQDN (the client’s NETBIOS domain name is considered trusted). For example, \\srv1.woshub.com\apps\file.exe or \\192.168.123.45\apps\file.exe
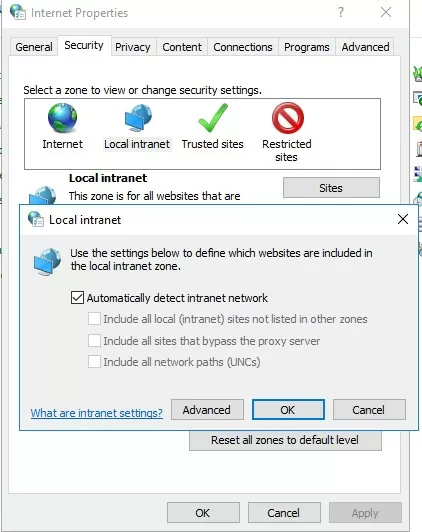
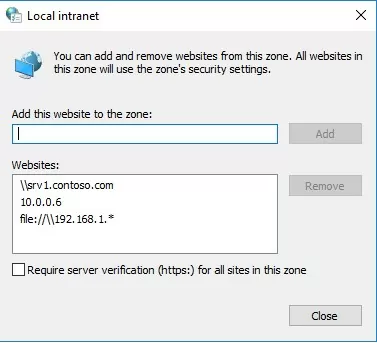
To make a server address trusted, add its name and/or the IP address of the remote server ( or NAS storage) to the Local Intranet zone in the Internet Explorer settings.
- Go to Control Panel -> Internet Option (or run the
inetcpl.cplcommand) - Go to the Security tab;
- Open Local Intranet -> Sites -> Advanced
- Add a server name and/or IP address. For example,
\\10.0.0.6,\\srv.contoso.comor\\127.0.0.1\for a local computer. You can use a wildcard character. Wildcard character * can be used. For example, add all IP addresses in a specific subnet to the Local Intranet zone:file://192.168.1.*
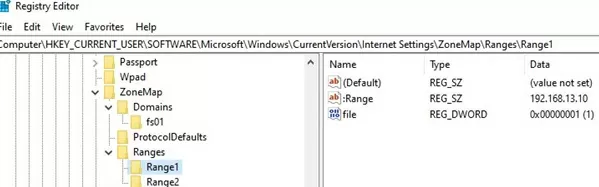
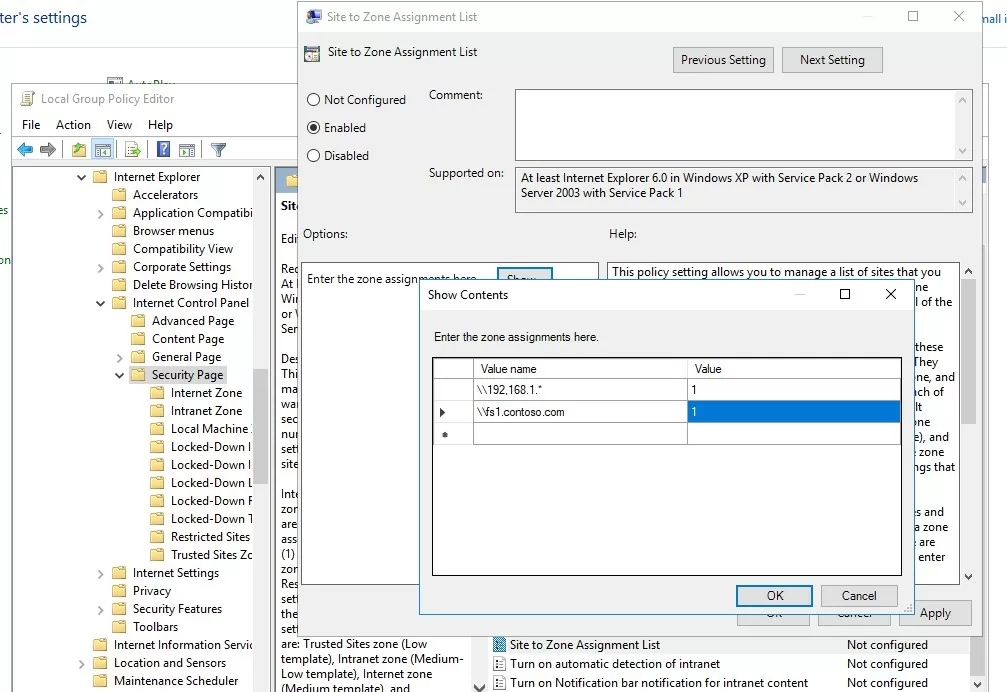
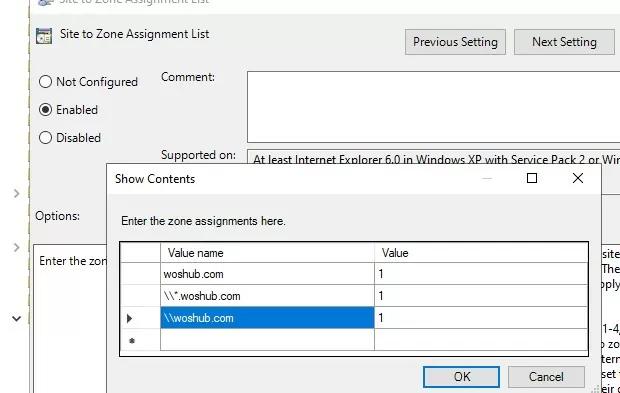
To add trusted addresses to the Local intranet zone on domain computers, you can use the GPO:
- Open the local (gpedit.msc) or domain (
gpmc.msc) Group Policy editor - Go to Computer Configuration -> Administrative Templates -> Windows Components -> Internet Explorer -> Internet Control Panel -> Security Page
- Enable the policy Site to Zone Assignment List. Specify a list of trusted hosts/domains/ IP addresses in the following format in the policy settings:
- Save the policy changes and update the GPO settings on the client computer (
gpupdate /force).
No security warning appears when opening executables from shared folders on hosts that have been added to the Local intranet zone.
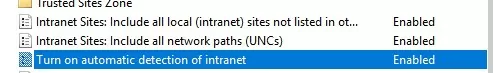
To automatically detect host addresses in the Intranet zone, enable the following Group Policy settings in User Configuration -> Administrative Templates -> Windows Components -> Internet Explorer -> Internet Control Panel -> Security Page.
- Intranet Sites: Include all local (intranet) sites not listed in other zones
- Intranet Sites: Include all network paths (UNCs)
- Turn on automatic detection of intranet
Open File Security Warning When Using Roaming Folders
If you are using AppData folder redirection (roaming profile scenarios), users may encounter the ‘Open File – Security Warning’ prompt when launching app shortcuts from their profile folders.
In this case, add the server (or the entire domain) where roaming profiles are stored to the IE trusted zone.
Use the GPO option: User Configuration -> Policies -> Administrative Templates -> Windows Components -> Internet Explorer -> Internet Control Panel -> Security Page -> Site to Zone Assignment List. Add server (domain) name with value 1.
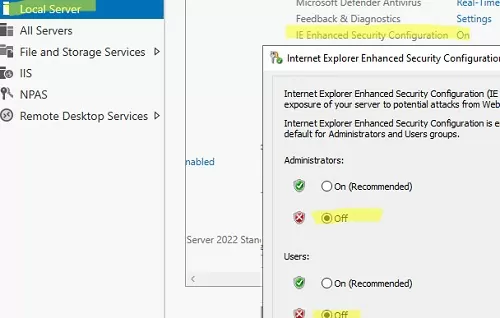
On Windows Server hosts with the RDS role, in some cases, only disabling IE Enhanced Security will help to get rid of these warnings.
- Open the Server Manager -> Local Server.
- Click the IE Enhanced Security Configuration option
- Turn off enhanced security for users and administrators.
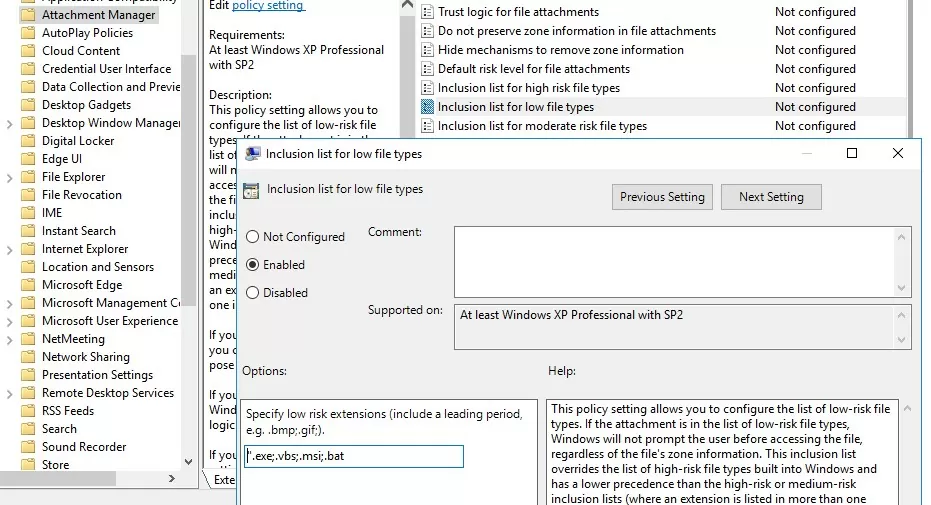
Disable Open File Security Warning for Specific File Types via GPO
Sometimes, it can be useful to disable the security warning for certain file types (extensions) using Group Policies. However, for security reasons, the list of allowed file extensions should be kept to a minimum.
To do it, in the GPO Editor, go to User Configuration-> Administrative Templates-> Windows Components-> Attachment Manager.
- Enable the policy Do not preserve zone information in file attachments. All executable files downloaded from the Internet are allowed without confirmation.
- Enable the policy Inclusion list for low file types. In the policy settings, specify the file extensions for which the security warning prompt should be disabled. e.g,
.exe; .vbs; .msi. Windows will ignore alternate data stream markers on files with these extensions and run them without warning.Note. This policy adds file extensions to the LowRiskFileTypes registry parameter:[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Associations] "LowRiskFileTypes"=".exe;.vbs;.msi;.bat;"
After applying the policy, the security window no longer appears when opening executable files with the specified extensions (regardless of whether the NTFS Zone.Identifier stream exists).
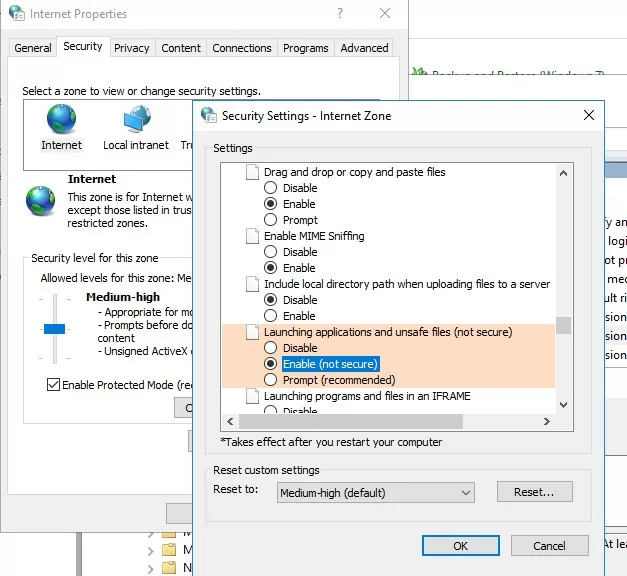
The last (but less secure) option is to allow running any file from the Internet in the Internet Options for the Internet zone: Security -> Internet -> Custom level -> Miscellaneous -> Launching applications and unsafe files (not secure) -> Enable.
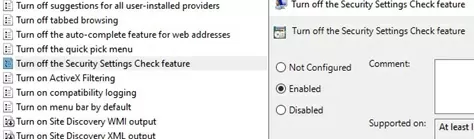
You can completely disable the “Open File – Security Warning” prompt for unsafe files using the GPO option Turn off the Security Settings Check feature (Computer Configuration -> Administrative Templates -> Windows Components -> Internet Explorer).
Or use the following commands:
REG ADD "HKLM\SOFTWARE\Policies\Microsoft\Internet Explorer\Security" /V "DisableSecuritySettingsCheck" /T "REG_DWORD" /D "00000001" /F
REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3" /V "1806" /T "REG_DWORD" /D "00000000" /F
REG ADD "HKLM\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3" /V "1806" /T "REG_DWORD" /D "00000000" /F
6 comments
There is no unblock option 🙁
Thank you for explaining the “fix” for this…worked fine for me using Windows 7 Pro. It just started after the last Windows update a couple of days ago.
Not an issue any more…”UNBLOCKED”…!!!
Thanks again and have a great day…!
Works very well, thanks!
Thank you.
Best regards. Aleksej
As usual, incredibly useful information. Just enabling the policy “Turn on automatic detection of intranet” as suggested removed the pop up warnings from my domain environment.
What made this problem additionally frustrating, is that when attempting to install applications stored on a file server using the Start-Process cmdlet via Powershell remoting to a target workstation, the command just hangs infinitely because of this security warning!
Thanks again!
Firefox seems to have stopped taking “browser.download.saveZoneInformation” into account for some time (since version 29?) and instead relies on the Windows “SaveZoneInformation” registry value.