Java Runtime Environment (JRE) is widely used on user computers to run different enterprise Java apps . However, some apps require the specific Java version and may work incorrectly in other versions. In this article we will discuss how to check Java versions installed on computers in your network, and how to uninstall or update JRE using PowerShell.
How to Check Java Version in Windows?
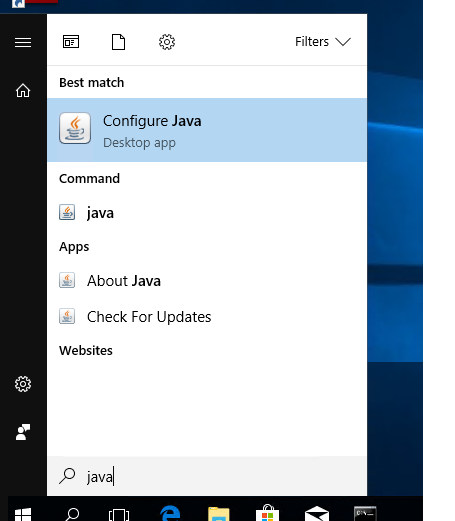
You can get the version number of Java installed on your computer if you enter java in Windows 10 search box and run Java applet.
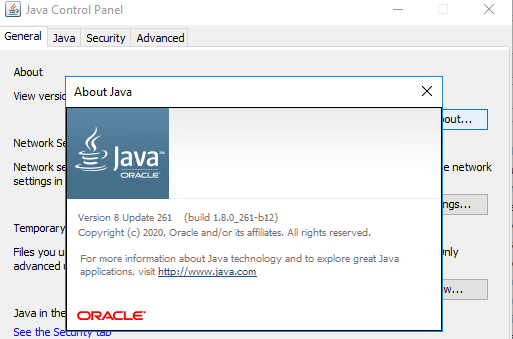
In About Java window, the current JRE version is specified. In my case, it is Java Version 8 Update 261 (build 1.8.0_261-b12). Note the value of the JRE build. All Java versions have 1 in the beginning followed by the number of major JRE version (it is 8 in my case) and the update number.
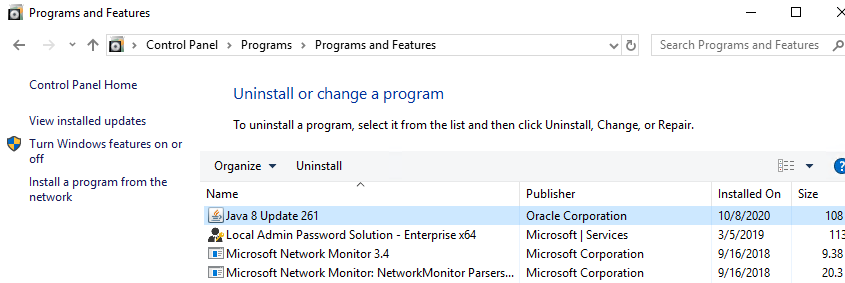
You can also check the current Java version in Windows Program and Features (Win+R -> appwiz.cpl).
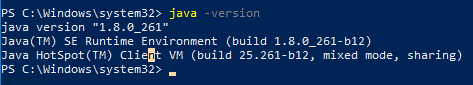
You can display the current Java version in the command prompt. Run cmd.exe and run the command:
java -version
java version "1.8.0_261" Java(TM) SE Runtime Environment (build 1.8.0_261-b12) Java HotSpot(TM) Client VM (build 25.261-b12, mixed mode, sharing)
Check Java Version using PowerShell
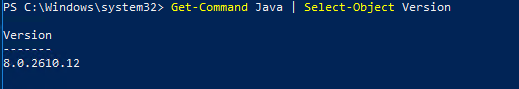
You can check Java version installed on your computer using PowerShell. You can just check the version of the executable file java.exe (the path to it is set in the environment variables when JRE SE is installed on your computer). Display the java file version:
Get-Command Java | Select-Object Version
You can view detailed information about Java version, update and release number:
Get-Command java | Select-Object -ExpandProperty Version
Major Minor Build Revision ----- ----- ----- -------- 8 0 2610 12
If you want to get a string value of your Java version to be used in scripts, use the command:
(Get-Command java | Select-Object -ExpandProperty Version).tostring()
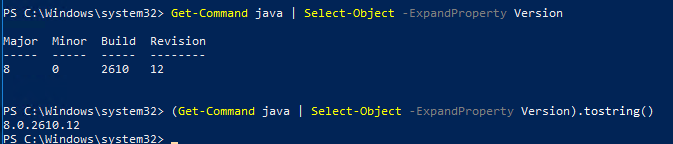
You can also find out your Java version through the WMI class Win32_Product (contains the list of installed programs in Windows):
Get-WmiObject -Class Win32_Product -Filter "Name like '%Java%'"
IdentifyingNumber : {26A24AE4-039D-4CA4-87B4-2F32180261F0}
Name : Java 8 Update 261
Vendor : Oracle Corporation
Version : 8.0.2610.12
Caption : Java 8 Update 261
IdentifyingNumber : {4A03706F-666A-4037-7777-5F2748764D10}
Name : Java Auto Updater
Vendor : Oracle Corporation
Version : 2.8.261.12
Caption : Java Auto UpdaterThe IDs may be used later to correctly uninstall JRE.
If you want to display only Java version without Java Auto Updater, use the following command:
Get-WmiObject -Class Win32_Product -Filter "Name like '%Java%' and not Name like '%Java Auto Updater%'" | Select -Expand Version
PowerShell – Check Java Version on Remote Computers
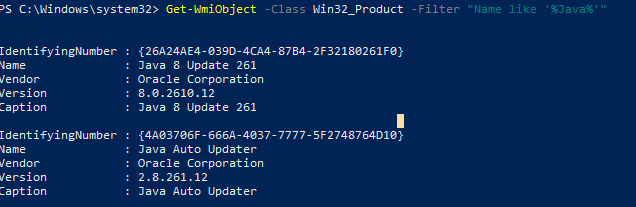
If you want to get Java versions used on all computers or servers in your domain, you can use the following PowerShell script. The script can get the information from all servers remotely according to the list you enter manually or from a text file. You can also get the list of servers or computers in AD using the Get-ADComputer cmdlet from the RSAT-AD-PowerShell module.
# PowerShell script to check Java SE (JRE) version on remote computers
# To check Java version on the computers in the list
# $computers = @('mun-sql01,mun-fs01,mun-sql02')
# Check Java version against the list of servers in a text file
#$computers=Get-content C:\PS\ServerList.txt
# To get Java version on all Windows Servers in AD domain
$computers = ((get-adcomputer -Filter { enabled -eq “true” -and OperatingSystem -Like ‘*Windows Server*’ }).name).tostring()
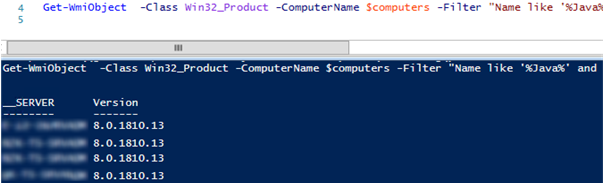
Get-WmiObject -Class Win32_Product -ComputerName $computers -Filter “Name like ‘%Java%’ and not Name like ‘%Java Auto Updater%'” | Select __Server, Version
As a result, you will have a table with the list of computers/servers and Java versions installed on them.
PowerShell Script to Uninstall All Java Versions
Why may you need to uninstall previous Java versions in Windows?
- Before you install a new Java version, it is better to uninstall all previous versions. Like in other products, new features appear and critical exploits are constantly fixed in Java. If you have older versions of Java installed, your computer is subject to infection or exploitation of known or 0-day vulnerabilities. Java has a built-in autoupdate mechanism, but on different reasons administrators may disable it on domain computers.
- You have no paid Java JRE subscription. In 2019, Oracle changed Java licensing policy. If you want to use previous Oracle JDK (Java SE) versions, you must get a paid subscription. It refers to all Java JRE releases after April, 16, 2019 (from Java 8 SE Update 211).Commercial Java SE versions have a long-time support (updates are released for 5 years since the release date). A free Java version is Open JDK (distributed under GPL), but you have to update it every six months. Another Open JDK disadvantage is that it doesn’t have a convenient installer for Windows. You must download and install Open JDK manually. There is a nice option to install Open JDK using the WinGet package manager:
winget install --id=ojdkbuild.openjdk.11.jdk -e
You can use the following PowerShell script to remove all installed Java versions on a local computer:
$jre_installed = Get-WmiObject -Class Win32_Product -Filter "Name like '%Java%'"
$jre_installed.Uninstall()
However, the uninstall command above is based on WMI and works slowly.
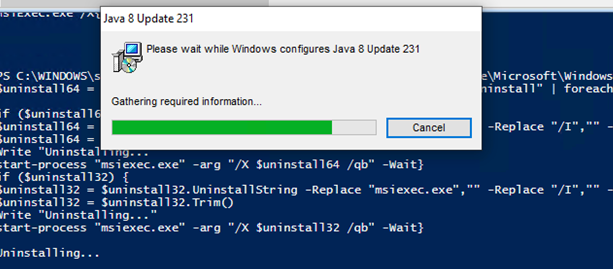
Instead, you can get a list of installed Java versions from the registry and uninstall all of them by their product GUID generated when you install software via MSI.
#PowerShell script to uninstall all Java SE (JRE) versions on a computer
$uninstall32 = gci "HKLM:\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall" | foreach { gp $_.PSPath } | ? { $_ -like "*Java*" } | select UninstallString
$uninstall64 = gci "HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall" | foreach { gp $_.PSPath } | ? { $_ -like "*Java*" } | select UninstallString
# Uninstall 64-bit Java versions
if ($uninstall64) {
$uninstall64 = $uninstall64.UninstallString -Replace "msiexec.exe", "" -Replace "/I", "" -Replace "/X", ""
$uninstall64 = $uninstall64.Trim()
Write "Uninstalling Java ..."
start-process "msiexec.exe" -arg "/X $uninstall64 /qb" -Wait
}
# Uninstall 32-bit Java versions
if ($uninstall32) {
$uninstall32 = $uninstall32.UninstallString -Replace "msiexec.exe","" -Replace "/I","" -Replace "/X",""
$uninstall32 = $uninstall32.Trim()
Write "Uninstalling all Java SE versions..."
start-process "msiexec.exe" -arg "/X $uninstall32 /qb" -Wait
}
How to Download and Install Java JRE Using PowerShell?
The following PowerShell script automatically downloads the latest version of Java installer from the official website and installs it on a computer(you can download both online and offline installer). The install command suppress reboot request and disables automatic Java updates.
# PowerShell script to automatically download and install the latest Java SE (JRE) version
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
# Download an online Java installer
$URL = (Invoke-WebRequest -UseBasicParsing https://www.java.com/en/download/manual.jsp).Content | % { [regex]::matches($_, '(?:<a title="Download Java software for Windows Online" href=")(.*)(?:">)').Groups[1].Value }
# Download an offline Java installer
#$URL = (Invoke-WebRequest -UseBasicParsing https://www.java.com/en/download/manual.jsp).Content | % { [regex]::matches($_, '(?:<a title="Download Java software for Windows Offline" href=")(.*)(?:">)').Groups[1].Value }
Invoke-WebRequest -UseBasicParsing -OutFile jre8.exe $URL
Start-Process .\jre8.exe '/s REBOOT=0 SPONSORS=0 AUTO_UPDATE=0' -wait
echo $?
Invoke-WebRequest: The request was aborted: Could not create SSL/TLS secure channel.
The script will automatically download a Java installation file, save it on a disk as jre8.exe and install.
4 comments
Excellent article. Thank you so much for sharing with us!
When uninstalling JRE, it helps to use Publisher in your filter, otherwise your results include apps like Notepad++ that use the Uninstall reg key to store app configs that include the term “Java”.
$uninstall32 = gci “HKLM:\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall” | foreach { gp $_.PSPath } | ? { $_ -like “*Java*” -and $_.Publisher -like “*Oracle*” } | select UninstallString
$uninstall64 = gci “HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall” | foreach { gp $_.PSPath } | ? { $_ -like “*Java*” -and $_.Publisher -like “*Oracle*” } | select UninstallString
Updated:
And filter out blank entries where no UninstallString was found.
$uninstalllist = $null
$uninstall = gci “HKLM:\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall” | foreach { gp $_.PSPath } | ? { $_ -like “*Java*” -and $_.Publisher -like “*Oracle*” } | select UninstallString
$uninstall += gci “HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall” | foreach { gp $_.PSPath } | ? { $_ -like “*Java*” -and $_.Publisher -like “*Oracle*” } | select UninstallString
$uninstalllist = $uninstall.Where({$_.UninstallString -ne $null})
# Uninstall all Java versions
if ($uninstalllist) {
foreach ($cmdline in $uninstalllist) {
$guid = ($cmdline.UninstallString -Replace “msiexec.exe”, “” -Replace “/I”, “” -Replace “/X”, “”).Trim()
start-process “msiexec.exe” -arg “/X $guid /qn” -Wait
}
}
HI
Do you know how to update the Java runtime from the BIOS?