The latest versions of Windows support the DNS over HTTPS (DoH) protocol, which allows domain name resolution (DNS queries) to be performed over an encrypted HTTPS connection. In this article, we’ll look at what the DNS over HTTPS protocol is used for, and how to use it in Windows.
How to Enable DNS over HTTPS from the Windows GUI
Windows 11 and Windows Server 2022 have built-in DNS-over-HTTPS (DoH) support in the DNS client. The client will use DoH to encrypt DNS traffic if you have specified the IP address of the DNS server that supports DoH in the settings of the network adapter.
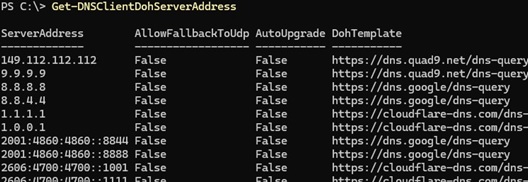
Use PowerShell to list the IP addresses of public DNS servers that support DoH:
Get-DNSClientDohServerAddress
| Provider | IP addresses of public DNS servers supporting DNS-over-HTTPS |
| Cloudflare | 1.1.1.1, 1.0.0.1 |
| 8.8.8.8, 8.8.4.4 | |
| Quad9 | 9.9.9.9, 149.112.112.112 |
Specify the IPv4 or IPv6 address of one of these DNS servers in the network interface settings (or the address of an alternative DNS server with DoH support, after you have added it as described below.)
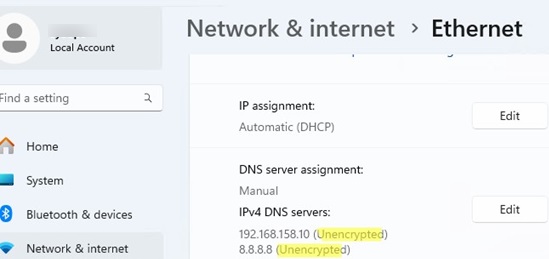
- Navigate to Settings -> Network & Internet -> Ethernet (or Wi-Fi)
- DNS traffic is not encrypted in this case.
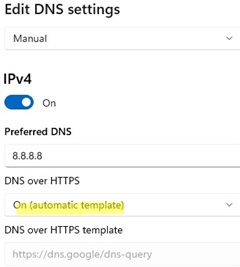
- Click the Edit
- Enter the IP address of the DNS server and select -> On (automatic template) for the DNS over HTTPS parameter.
- Save the changes. Now the DNS queries from the computer will be encrypted.
Windows Server 2022 DNS client also supports DoH (however, the DNS Server service itself does not support DoH in this release.).
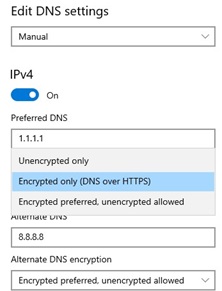
Specify the DNS server IP address in the network interface settings and enable the Encrypted only (DNS over HTTPS) mode.
$AutoDohPath = 'HKLM:\SYSTEM\CurrentControlSet\Services\Dnscache\Parameters'
$AutoDohKey = 'EnableAutoDoh'
New-ItemProperty -Path $AutoDohPath -Name $AutoDohKey -Value 2 -PropertyType DWord -Force
However, this feature has not been implemented in the final release of Windows 10!
DNS over HTTPS Configuration on Windows 11 via Command Prompt
On Windows, you can use the command line interface to enable and configure DNS over HTTPS.
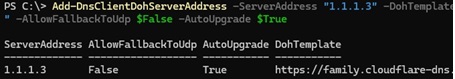
First, add the IP address of the DoH server to the list of known DNS servers. For example, to add Cloudflare Family alternative DNS servers 1.1.1.3 and 1.0.0.3 (used to filter malware and adult content), run:
$DNSServer="1.1.1.3"
Add-DnsClientDohServerAddress -ServerAddress $DNSServer -DohTemplate "https://family.cloudflare-dns.com/dns-query" -AllowFallbackToUdp $False -AutoUpgrade $True
After you register the template for the DoH DNS server, assign that IP as the preferred DNS server in the network interface settings using the following PowerShell command:
Set-DnsClientServerAddress Ethernet0 -ServerAddresses ($DNSServer)
Then enable mandatory use of DNS over HTTPS for the network interface:
$i = Get-NetAdapter -Physical -Name Ethernet0
$s1 = "HKLM:System\CurrentControlSet\Services\Dnscache\InterfaceSpecificParameters\" + $i.InterfaceGuid + "\DohInterfaceSettings\Doh\$DNSServer"
New-Item -Path $s1 -Force | New-ItemProperty -Name "DohFlags" -Value 1 -PropertyType QWORD
Clear-DnsClientCache
Or use a separate GPO setting to enforce using DoH:
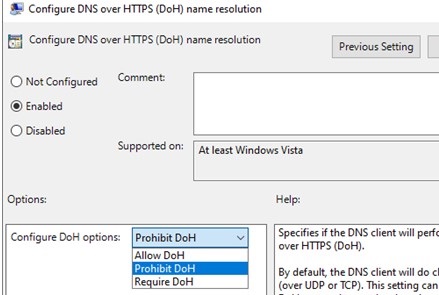
- Open the local GPO editor (
gpedit.msc) - Navigate to Computer Configuration -> Policies -> Administrative Templates -> Network -> DNS Client section
- Enable the policy Configure DNS over HTTPS (DoH) name resolution and set the value to Require DoH.
How to verify that DNS over HTTPS works on Windows
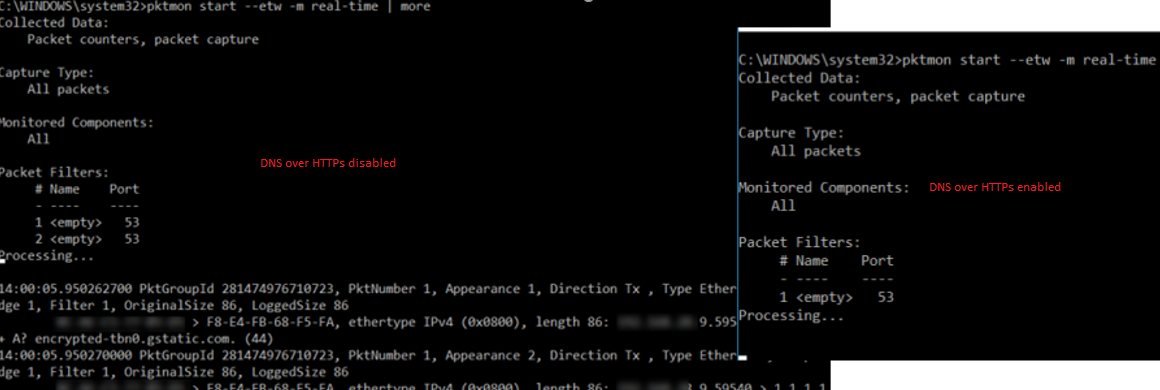
To verify that the DNS client is using the encrypted HTTPS (443) protocol for name resolution instead of the default UDP/TCP port 53, use the built-in network traffic capture tool named PktMon.exe.
Remove all current Packet Monitor filters:
pktmon filter remove
Create a new filter for the default DNS port (53):
pktmon filter add -p 53
Start real-time traffic monitoring (traffic will be output to the console):
pktmon start --etw -m real-time
There should be no traffic on port 53 if you have properly configured DNS over HTTPS. This means that all DNS queries are sent in an encrypted HTTPS session (the screenshot below shows the console output with DoH disabled and enabled).
DNS over HTTPS support is implemented in all popular browsers (Google Chrome, Mozilla Firefox, Microsoft Edge, Opera). You can enable DoH support in any of them. This encrypts your browser’s DNS queries (DNS traffic from other apps will still sent as plain text).
DNS over HTTPS and DNS over TLS will cause problems for corporate network administrators by making it more difficult to restrict access to external resources from internal networks.


9 comments
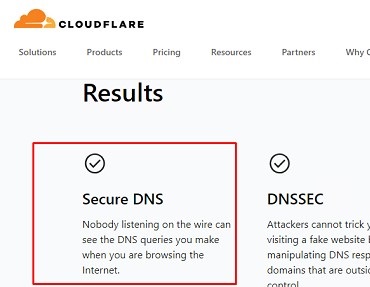
A correction to the last screenshot, DNSSEC is not the same as DNS-over-HTTPS. DNSSEC is for server-to-server, and DoT is for server-to-client. The Cloudflare web site is confirming that the Windows 10 is using DoT to communicate to its DNS resolver, and its DNS resolver has implemented the server-side DNSSEC features. The page is correct, you just need to highlight the Secure DNS box rather than the DNSSEC box.
Hello,
Thanks for your article. But It doesn’t work on my computer : there is always traffic on DNS port (53) even with a value of 2 for EnableAutoDoh, a good DNS (1.1.1.1) and after restart the computer.
Have you got an idea to resolve this ?
Thanks.
“Create a new DWORD parameter with the name EnableAutoDoh and value 2; ‘
Can we set this to 3 ???
Doesn’t work with 21H1 in case anyone is trying. Probably need to wait till next year for the Public builds to get this.
One question: Does the Windows Server 2022 DNS server support DNS over HTTPS (DoH)?
In an active directory network, all computers added to the domain have Active Directory DNS Server configured in the DNS client.
If I configure DNS over HTTPS (DoH) in the client but the Active Directory DNS Server does not support it …
You can only use DoH DNS client on Windows Server 2022:
DNS Client in Windows Server 2022 now supports DNS-over-HTTPS (DoH) which encrypts DNS queries using the HTTPS protocol. This helps keep your traffic as private as possible by preventing eavesdropping and your DNS data being manipulated. Learn more about configuring the DNS client to use DoH. https://docs.microsoft.com/en-us/windows-server/networking/dns/doh-client-supportWindows 10 does not support DNS over HTTPS and it doesn’t look like it ever will.
Very Good Post . It Solved My Problem After Changing Internet Connection.